More than 900,000 customers of German ISP Deutsche Telekom (DT) were knocked offline this week after their Internet routers got infected by a new variant of a computer worm known as Mirai. The malware wriggled inside the routers via a newly discovered vulnerability in a feature that allows ISPs to remotely upgrade the firmware on the devices. But the new Mirai malware turns that feature off once it infests a device, complicating DT’s cleanup and restoration efforts. Security experts say the multi-day outage is a sign of things to come as cyber criminals continue to aggressively scour the Internet of Things (IoT) for vulnerable and poorly-secured routers, Internet-connected cameras and digital video recorders (DVRs). Once enslaved, the IoT devices can be used and rented out for a variety of purposes — from conducting massive denial-of-service attacks capable of knocking large Web sites offline to helping cybercriminals stay anonymous online. This new variant of Mirai builds on malware source code released at the end of September. That leak came a little more a week after a botnet based on Mirai was used in a record-sized attack that caused KrebsOnSecurity to go offline for several days. Since then, dozens of new Mirai botnets have emerged, all competing for a finite pool of vulnerable IoT systems that can be infected. Until this week, all Mirai botnets scanned for the same 60+ factory default usernames and passwords used by millions of IoT devices. But the criminals behind one of the larger Mirai botnets apparently decided to add a new weapon to their arsenal, incorporating exploit code published earlier this month for a security flaw in specific routers made by Zyxel and Speedport. These companies act as original equipment manufacturers (OEMs) that specialize in building DSL modems that ISPs then ship to customers. The vulnerability exists in communications protocols supported by the devices that ISPs can use to remotely manage all of the customer-premises routers on their network. According to BadCyber.com, which first blogged about the emergence of the new Mirai variant, part of the problem is that Deutsche Telekom does not appear to have followed the best practice of blocking the rest of the world from remotely managing these devices as well. “The malware itself is really friendly as it closes the vulnerability once the router is infected,” BadCyber noted. “It performs [a] command which should make the device ‘secure,’ until next reboot. The first one closes port 7547 and the second one kills the telnet service, making it really hard for the ISP to update the device remotely.” [For the Geek Factor 5 readership out there, the flaw stems from the way these routers parse incoming traffic destined for Port 7547using communications protocols known as TR-069]. DT has been urging customers who are having trouble to briefly disconnect and then reconnect the routers, a process which wipes the malware from the device’s memory. The devices should then be able to receive a new update from DT that plugs the vulnerability. That is, unless the new Mirai strain gets to them first. Johannes Ullrich , dean of security research at The SANS Technology Institute , said this version of Mirai aggressively scans the Internet for new victims, and that SANS’s research has shown vulnerable devices are compromised by the new Mirai variant within five to ten minutes of being plugged into the Internet. Ullrich said the scanning activity conducted by the new Mirai variant is so aggressive that it can create hangups and crashes even for routers that are are not vulnerable to this exploit. “Some of these devices went down because of the sheer number of incoming connections” from the new Mirai variant, Ullrich said. “They were listening on Port 7547 but were not vulnerable to this exploit and were still overloaded with the number of connections to that port.” FEEDING THE CRIME MACHINE Allison Nixon , director of security research at Flashpoint, said this latest Mirai variant appears to be an attempt to feed fresh victims into one of the larger and more established Mirai botnets out there today. Nixon said she suspects this particular botnet is being rented out in discrete chunks to other cybercriminals. Her suspicions are based in part on the fact that the malware phones home to a range of some 256 Internet addresses that for months someone has purchased for the sole purpose of hosting nothing but servers used to control multiple Mirai botnets. “The malware points to some [Internet addresses] that are in ranges which were purchased for the express purpose of running Mirai,” Nixon said. “That range does nothing but run Mirai control servers on it, and they’ve been doing it for a while now. I would say this is probably part of a commercial service because purchasing this much infrastructure is not cheap. And you generally don’t see people doing this for kicks, you see them doing it for money.” Nixon said the criminals behind this new Mirai variant are busy subdividing their botnet — thought to be composed of several hundred thousand hacked IoT devices — among multiple, distinct control servers. This approach, she said, addresses two major concerns among cybercriminals who specialize in building botnets that are resold for use in huge distributed denial of service (DDoS) attacks. The first is that extended DDoS attacks which leverage firepower from more bots than are necessary to take down a target host can cause the crime machine’s overall bot count to dwindle more quickly than the botnet can replenish itself with newly infected IoT devices — greatly diminishing the crime machine’s strength and earning power. “I’ve been watching a lot of chatter in the DDoS community, and one of the topics that frequently comes up is that there are many botnets out there where the people running them don’t know each other, they’ve just purchased time on the botnet and have been assigned specific slots on it,” Nixon said. “Long attacks would end up causing the malware or infected machines to crash, and the attack and would end up killing the botnet if it was overused. Now it looks like someone has architected a response to that concern, knowing that you have to preserve bots as much as you can and not be excessive with the DDoS traffic you’re pushing.” Nixon said dividing the Mirai botnet into smaller sections which each answer to multiple control servers also makes the overall crime machine more resistant to takedown efforts by security firms and researchers. “This is an interesting development because a lot of the response to Mirai lately has been to find a Mirai controller and take it down,” Nixon said. “Right now, the amount of redundant infrastructure these Mirai actors have is pretty significant, and it suggests they’re trying to make their botnets more difficult to take down.” Nixon said she worries that the aggressive Mirai takedown efforts by the security community may soon prompt the crooks to adopt far more sophisticated and resilient methods of keeping their crime machines online. “We have to realize that the takedown option is not going to be there forever with these IoT botnets,” she said. Source: https://krebsonsecurity.com/2016/11/new-mirai-worm-knocks-900k-germans-offline/
View article:
New Mirai Worm Knocks 900K Germans Offline


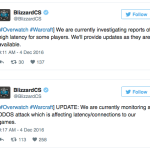 Miscreants have struck Blizzard servers again with multiple waves of DDoS attacks over the last 12 hours. Warcraft and Overwatch, two massively popular games, have been facing latency, login and disconnection issues even while Blizzard has been working on fixing the problem. The company first acknowledged the problem in a tweet Sunday evening. Since then, Blizzard claimed to have regained control over matters at its end, only to announce twice the DDoS attacks had restarted. Its last update, at 11:42 p.m. EST Sunday, came three hours after the last wave of DDoS attacks. On Twitter, a group calling itself Phantom Squad claimed responsibility for the attack Blizzard also provided a link to a support page on its website that may help some users troubleshoot their connection problems. As always, social media was abuzz with users venting their frustration at the gaming servers being affected. This is at least the fifth such instance in the last few months. The company also has a scheduled maintenance coming up Tuesday. Source: http://www.ibtimes.com/warcraft-overwatch-down-blizzard-ddos-attacks-affect-gaming-service-2454782
Miscreants have struck Blizzard servers again with multiple waves of DDoS attacks over the last 12 hours. Warcraft and Overwatch, two massively popular games, have been facing latency, login and disconnection issues even while Blizzard has been working on fixing the problem. The company first acknowledged the problem in a tweet Sunday evening. Since then, Blizzard claimed to have regained control over matters at its end, only to announce twice the DDoS attacks had restarted. Its last update, at 11:42 p.m. EST Sunday, came three hours after the last wave of DDoS attacks. On Twitter, a group calling itself Phantom Squad claimed responsibility for the attack Blizzard also provided a link to a support page on its website that may help some users troubleshoot their connection problems. As always, social media was abuzz with users venting their frustration at the gaming servers being affected. This is at least the fifth such instance in the last few months. The company also has a scheduled maintenance coming up Tuesday. Source: http://www.ibtimes.com/warcraft-overwatch-down-blizzard-ddos-attacks-affect-gaming-service-2454782