What do cyber-attacks have in common with hurricanes, tornados and earthquakes? All are realities in our world. No matter how common or uncommon they may be, failing to prepare for any of them will lead to costs that could be unbearable—or worse. These were the thoughts of Nikhil Taneja, MD Radware as he shared the company’s annual Global Application & Network Security Report 2016-17 that identifies major attack trends of 2016, outlines industry preparedness, and offers predictions for in 2017. The report finds that 98% of Organizations Experienced Attacks in 2016, indicating that cyber-attacks became a way of life for nearly every organization in 2016. This trend will continue in 2017, predicts Radware. While understanding some crucial aspects such as The threat landscape—who the attackers are, their motives and tools, what will be the potential impact on businesses, including associated costs of different cyber-attacks, how a company’s preparedness level compares to other organizations etc, the report comes up with some of the key findings: – IoT Botnets Open the 1TBps Floodgates- This exemplifies why preparing for “common” attacks is no longer enough. This event introduced sophisticated vectors, such as GRE floods and DNS water torture. – Cyber-Ransom Proves Easiest, Most Lucrative Tool for Cybercriminals- Almost all ransom events have a different attack vector, technique or angle. There are hundreds of encrypting malware types, many of which were developed and discovered this year as part of the hype. Also, DDoS for ransom groups are professionals who leverage a set of network and application attacks to demonstrate their intentions and power. – Cyber-Attacks Cost Almost Twice What You May Think- Most companies have not come up with a precise calculation of the losses associated with a cyber-attack. Those who have quantified the losses estimate the damage at nearly double the amount compared to those who estimate. – Stateful Devices: #1 Point of Failure- Common IT devices, including firewalls, application delivery controllers and intrusion protection systems, now represent the greatest risk for an outage. Consequently, they require a dedicated attack mitigation solution to protect them. Threat Landscape Trends The report identifies top five trends that dominated 2016 threat landscape and will continue to haunt CISOs in the coming years. These include: – Data Leakage + SLA Impact Are Top Concerns – Data leakage and service level impact often come together, with a DDoS attack serving as a smokescreen that distracts IT teams so data can be infiltrated. – Mirai Rewrites the Rules- As the first IoT open-source botnet, Mirai is changing the rules of real-time mitigation and makes security automation a must. It isn’t just that IoT botnets can facilitate sophisticated L7 attack launches in high volumes. The fact that Mirai is open-source code means hackers can potentially mutate and customize it—resulting in an untold variety of new attack tools that can be detected only through intelligent automation. – Non-Volumetric DoS: Alive and Kicking – Despite astonishing volumes, neither the number of victims nor the frequency of attacks has grown. Most non-volumetric DDoS attacks are in relatively lower volumes, with 70% below 100Mbps. Rate-based security solutions continue to fall short, requiring companies to rethink their security strategy and embrace more sophisticated solutions. Without those upgrades, there is a good chance an organization will experience, yet lack visibility into service degradation. – Increased Attacks against Governmental Institutions- 2016 brought a new level of politically affiliated cyber protests. While the U.S. presidential election was in the spotlight, the media reported on a different breach almost weekly. These incidents happened across the globe, with regimes suffering from cyber-attacks due to alleged corruption or perceived injustices. – SSL-Based Attacks Continue to Grow- Although 39% report suffering an SSL-based attack, only 25% confidently state they can mitigate it. – DDoS Attacks Are Becoming Shorter- Burst attacks are increasing thanks to their effectiveness against most mitigation solutions. Security Strategy Evolves Rather Slowly These trends and findings indicate that while hackers continue to develop new attack tools and techniques, 40% of organizations do not have an incident response plan in place. Seventy percent do not have cyber-insurance. And despite the prevalence of ransomware, only 7% keep Bitcoin on hand. Another interesting finding of the study was three-fourths of companies do not employ hackers in their security teams, and 43% say they could not cope with an attack campaign lasting more than 24 hours. “Combining statistical research and frontline experience, the Radware report identifies trends that can help educate the security community. It draws information from sources such as the information security industry survey, where this year, 598 individual respondents representing a wide variety of organizations around the world participated,” Taneja commented. On average, responding organizations have annual revenue of USD $1.9 billion and about 3,000 employees. Ten percent are large organizations with at least USD 5 billion in annual revenue. Respondents represent more than 12 industries, with the largest number coming from the following: professional services and consulting (15%), high tech products and services (15%), banking and financial services (12%) and education (9%), the study notes. Source: http://www.cxotoday.com/story/cyber-attacks-cost-almost-twice-what-you-may-think/
Continue reading here:
Cyber-Attacks Cost Almost Twice What You May Think


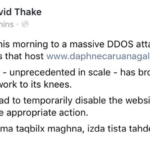 The servers hosting Daphne Caruana Galizia’s personal blog have suffered a DDoS attack. A DDos (denial of service) attack occurs when many systems flood the bandwidth of a targeted system, in an attempt to make the online service unavailable. Mrs Caruana Galizia does not yet know who is behind the attack, but did say it is highly likely to be a person of Maltese nationality.. Prior to the DDoS attack on the servers, she said, a fake Gmail account was setup – similar to her personal email address. The person who created the account, then emailed two persons working for the company who handle software support for the website, and tried to acquire information required to hack the site through them. This, however, did not work and the software support personnel realised that it was not Mrs Caruana Galizia’s email address, and also the use of broken English in the email. This, she said, is what led her to believe that the person behind the attack is Maltese. The police were contacted aftewr the DDOS attack occurred later, and an investigation is ongoing. The fake Gmail address used a proxy server, and thus far no culprit has been identified, she said. She explained that aside from the crime involving the DDoS attack, impersonation is also a crime. Vanilla Communications, a server hosting company owned by David Thake, hosts Daphne Caruana Galizia’s personal blog – a service that she pays for each month, she said. In a Facebook post, Mr Thake said that the servers hosting her website suffered a DDoS attack which he called “unprecedented in scale.” Mr Thake, in his post, said the attack brought the network to its knees. Source: http://www.independent.com.mt/articles/2017-03-21/local-news/Servers-hosting-Daphne-Caruana-Galizia-s-website-suffer-unprecedented-DDOS-attack-6736171884
The servers hosting Daphne Caruana Galizia’s personal blog have suffered a DDoS attack. A DDos (denial of service) attack occurs when many systems flood the bandwidth of a targeted system, in an attempt to make the online service unavailable. Mrs Caruana Galizia does not yet know who is behind the attack, but did say it is highly likely to be a person of Maltese nationality.. Prior to the DDoS attack on the servers, she said, a fake Gmail account was setup – similar to her personal email address. The person who created the account, then emailed two persons working for the company who handle software support for the website, and tried to acquire information required to hack the site through them. This, however, did not work and the software support personnel realised that it was not Mrs Caruana Galizia’s email address, and also the use of broken English in the email. This, she said, is what led her to believe that the person behind the attack is Maltese. The police were contacted aftewr the DDOS attack occurred later, and an investigation is ongoing. The fake Gmail address used a proxy server, and thus far no culprit has been identified, she said. She explained that aside from the crime involving the DDoS attack, impersonation is also a crime. Vanilla Communications, a server hosting company owned by David Thake, hosts Daphne Caruana Galizia’s personal blog – a service that she pays for each month, she said. In a Facebook post, Mr Thake said that the servers hosting her website suffered a DDoS attack which he called “unprecedented in scale.” Mr Thake, in his post, said the attack brought the network to its knees. Source: http://www.independent.com.mt/articles/2017-03-21/local-news/Servers-hosting-Daphne-Caruana-Galizia-s-website-suffer-unprecedented-DDOS-attack-6736171884