Group has ties to the Darkhotel APT attacks Security researchers from Forcepoint say that a new botnet has slowly risen and grown to contain over 19,000 zombies all over the world, but predominantly in Asian countries. Named Jaku ( Star Wars reference alert — Jakku ), the botnet has made most of its victims in countries such as Japan and South Korea, which count 73 percent of all infections. Nevertheless, security experts claim they detected infections with Jaku’s malware in 134 different countries, even if sometimes they comprised one or two users. Jaku is one of the most sophisticated and resilient botnets around Researchers say that first signs of the botnet appeared last September, and in a six-month timeframe, Jaku grew tremendously compared to other similar threats. The group behind Jaku controls the botnet through multiple C&C (command-and-control) servers, most of which are located in countries in the APAC region, such as Singapore, Malaysia, and Thailand. In ordered to stay hidden from sight, the Jaku group deployed three different C&C mechanisms but also used obfuscated SQLite databases on the client-side to store configuration files. The Jaku botnet can be used to deliver spam, to launch DDoS attacks, but also to implement other types of malware. This second-stage delivery process occurs with the help of steganography, which crooks use to bundle their malicious code inside image files. Jaku infects users via poisoned torrent files Forcepoint says that infections usually takes place via malware-laced files shared via BitTorrent. The group usually goes after high-value targets but doesn’t mind if other users are infected as well. Security researchers say the group has shown interest in international Non-Governmental Organizations (NGOs), engineering companies, academic institutions, scientists and government employees. “The Jaku campaign has clear connections with the TTPs used by the threat actors discussed by Kaspersky in the Darkhotel investigations from November 2014,” Forcepoint researchers point out. The Darkhotel group was later known as Dark Seoul , and has recently been connected to hackers in North Korea, part of the Lazarus Group . Source: http://news.softpedia.com/news/new-jaku-botnet-already-has-19-000-zombies-ideal-for-spam-and-ddos-attacks-503689.shtml
Read the original post:
New Jaku Botnet Already Has 19,000 Zombies, Ideal for Spam and DDoS Attacks

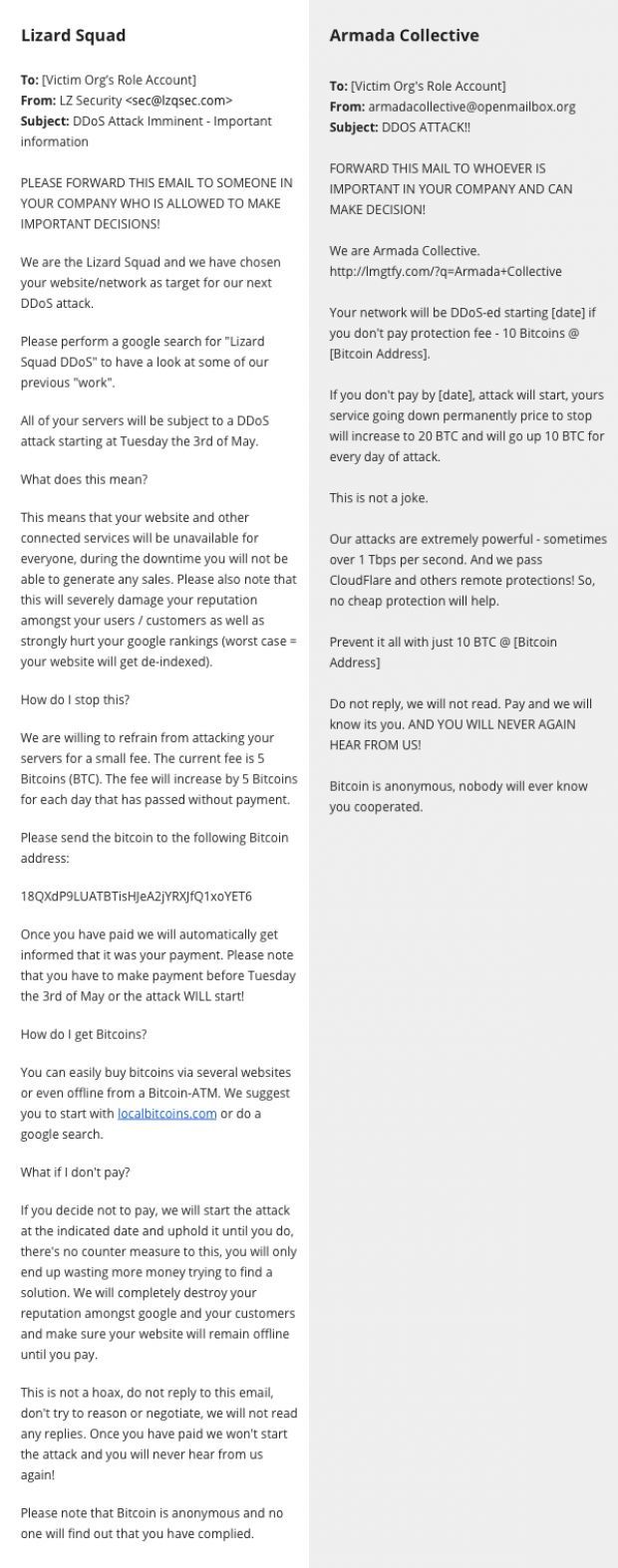
 After terrorizing companies under the fake Armada Collective moniker, the same group appears to have switched to using the name of the infamous Lizard Squad hacking crew, CloudFlare reported today. Early this week on Monday, CloudFlare let everyone know there was a criminal goup sending out extortion emails to companies around the globe. The criminals were posing as Armada Collective , an infamous group known for carrying out DDoS attacks if victims didn’t pay a so-called “protection tax.” The crooks were basing their attacks on the victims googling their name and finding out about the tactics of the real Armada Collective. In fact, CloudFlare says it never saw a single DDoS attack carried out by this group against its targets. In another blog post today, CloudFlare says that three days after they exposed the group, the criminals dropped the Armada Collective name and started using Lizard Squad instead, another hacking crew, famous for downing the Xbox and PlayStation networks on Christmas 2014. The change was to be expected since extorted organizations that would google the Armada Collective name would see all the stories about the copycats instead. CloudFlare says that over 500 companies received extortion emails from this group claiming to be Lizard Squad and that all these emails were identical. As before, the group used one single Bitcoin address to receive payments. By using one Bitcoin address, the group would not be able to tell which companies paid the ransom and which didn’t, meaning this was almost sure the same group as before, launching empty threats once again. CloudFlare says that just like when claiming to be Armada Collective, the group never launched any DDoS attacks when posing as Lizard Squad. Below is a comparison of the two ransom notes received by companies, from the fake Lizard Squad group on the left, and from the fake Armada Collective group on the right. Source: http://justfreedownload.net/news/98693/armada-collective-copycats-now-posing-as-lizard-squad-in-ddos-extortion-scheme.html
After terrorizing companies under the fake Armada Collective moniker, the same group appears to have switched to using the name of the infamous Lizard Squad hacking crew, CloudFlare reported today. Early this week on Monday, CloudFlare let everyone know there was a criminal goup sending out extortion emails to companies around the globe. The criminals were posing as Armada Collective , an infamous group known for carrying out DDoS attacks if victims didn’t pay a so-called “protection tax.” The crooks were basing their attacks on the victims googling their name and finding out about the tactics of the real Armada Collective. In fact, CloudFlare says it never saw a single DDoS attack carried out by this group against its targets. In another blog post today, CloudFlare says that three days after they exposed the group, the criminals dropped the Armada Collective name and started using Lizard Squad instead, another hacking crew, famous for downing the Xbox and PlayStation networks on Christmas 2014. The change was to be expected since extorted organizations that would google the Armada Collective name would see all the stories about the copycats instead. CloudFlare says that over 500 companies received extortion emails from this group claiming to be Lizard Squad and that all these emails were identical. As before, the group used one single Bitcoin address to receive payments. By using one Bitcoin address, the group would not be able to tell which companies paid the ransom and which didn’t, meaning this was almost sure the same group as before, launching empty threats once again. CloudFlare says that just like when claiming to be Armada Collective, the group never launched any DDoS attacks when posing as Lizard Squad. Below is a comparison of the two ransom notes received by companies, from the fake Lizard Squad group on the left, and from the fake Armada Collective group on the right. Source: http://justfreedownload.net/news/98693/armada-collective-copycats-now-posing-as-lizard-squad-in-ddos-extortion-scheme.html