![]() If you’ve attempted to access Themeforest or any other site on the Envato network lately, you may have encountered some down time. The company updated customers and community members today, attributing the technical difficulties to a DDoS attack: Since July 1, Envato has been the target of a sustained DDoS (distributed denial of service) attack. The attacker, whose motive and identity are unknown, has repeatedly flooded our servers with high levels of traffic, causing our services to be unavailable at various times. The most recent outage happened over the weekend when Envato Market was down for three hours on Friday and one hour on Sunday. This is a significant chunk of time for a market that paid out $224 million dollars to its members in 2014. The downtime has also impacted WordPress theme authors, who continue to dominate the Envato’s marketplace. According to Ben Chan, the company’s director of growth and revenue, 30 of the 31 sellers who make up the Power Elite wall of fame (selling $1 million+ worth of items) are WordPress product authors. The power of the WordPress economy on Envato is undeniable, but sales have taken a sharp decline in the past couple of months, even before the DDoS attack. According to PremiumWP, which cites reports from elite theme author Chris Robinson of Contempo and many others, sales have suddenly declined 50-70%. “Sales have declined over 70% starting from May with each passing day getting worse,” Robinson said in the members’ forum. “I’ve also spoken with other elite authors explaining the same thing. One example going from $1500/day to $700 – sure that’s still a great deal of money BUT what the hell is happening? “This isn’t just one or maybe twenty authors, it is marketplace wide affecting everyone. A marketplace wide decline in sales of this magnitude doesn’t just happen due to vacations, or other buyer factors. Going through the years of sales data (since 2008) this has never happened, I’ve personally gone from $2-3000/week to less than $700/week…that’s insane!” With new authors and products entering the market every day, the market share for established authors is slowly diminishing, but members are not convinced that this is the sole cause of the sharp drop in sales. FinalDestiny of TeoThemes, another author whose sales are declining, blames the one-size-fits-all theme products for gobbling up a greater slice of the market share. “Everybody is tired of these huge, monster multipurpose themes having the same price as normal themes, and that’s pretty much killing the marketplaces. But Envato couldn’t care less, as long as they get their share,” he said. In another thread, which ended up getting locked, there are 27 pages of comments from users speculating about why their sales have been dropping. Members cite seasonal buying fluctuations, piracy, Themeforest’s recent drop in Google search rankings, VAT and hidden price additions on checkout, and unfair pricing advantages for monster themes that claim to do everything, among other possible causes. In one thread, titled “More than 50% sales drop for most of the authors. Does TF care for Authors?“, an Envato community officer offered the following comment: We don’t really give sales updates over the forums other than to say your sales can go up and down for a multitude of reasons. Try not to assume the sky is falling every time the USA has a long weekend We have fast and slow periods throughout the year same as any business, and your portfolio will no doubt have peaks and valleys as well. This kind of generic reply has left theme authors scratching their heads, despite multiple threads in the forums popping up with concerns from those who are alarmed by the sudden drop. Many WordPress theme authors depend on Themeforest as their primary source of income. In one reply, the Aligator Studio seller sums up their concerns and frustration with the inability to convince Envato of the unusual circumstances that are affecting large numbers of sellers: We are not talking about valleys and peaks, we’re talking about a general traffic and sales fall, from New Year until now, especially after April. We’re not talking about regular ups and downs (sometimes steeper, sometimes not), due to longer weekends, summer holidays, and general and the usual stuff happening here in the last couple of years. It’s not a sky falling – it’s inability to pay our bills, we’re not fanatics that foresee the end of the world. Envato has yet to provide an official statement about the marketplace-wide decline in sales, apart from recognizing the network’s unavailability due to the recent DDoS attack. Source: http://wptavern.com/envato-targeted-by-ddos-attack-wordpress-theme-authors-report-major-decline-in-sales
If you’ve attempted to access Themeforest or any other site on the Envato network lately, you may have encountered some down time. The company updated customers and community members today, attributing the technical difficulties to a DDoS attack: Since July 1, Envato has been the target of a sustained DDoS (distributed denial of service) attack. The attacker, whose motive and identity are unknown, has repeatedly flooded our servers with high levels of traffic, causing our services to be unavailable at various times. The most recent outage happened over the weekend when Envato Market was down for three hours on Friday and one hour on Sunday. This is a significant chunk of time for a market that paid out $224 million dollars to its members in 2014. The downtime has also impacted WordPress theme authors, who continue to dominate the Envato’s marketplace. According to Ben Chan, the company’s director of growth and revenue, 30 of the 31 sellers who make up the Power Elite wall of fame (selling $1 million+ worth of items) are WordPress product authors. The power of the WordPress economy on Envato is undeniable, but sales have taken a sharp decline in the past couple of months, even before the DDoS attack. According to PremiumWP, which cites reports from elite theme author Chris Robinson of Contempo and many others, sales have suddenly declined 50-70%. “Sales have declined over 70% starting from May with each passing day getting worse,” Robinson said in the members’ forum. “I’ve also spoken with other elite authors explaining the same thing. One example going from $1500/day to $700 – sure that’s still a great deal of money BUT what the hell is happening? “This isn’t just one or maybe twenty authors, it is marketplace wide affecting everyone. A marketplace wide decline in sales of this magnitude doesn’t just happen due to vacations, or other buyer factors. Going through the years of sales data (since 2008) this has never happened, I’ve personally gone from $2-3000/week to less than $700/week…that’s insane!” With new authors and products entering the market every day, the market share for established authors is slowly diminishing, but members are not convinced that this is the sole cause of the sharp drop in sales. FinalDestiny of TeoThemes, another author whose sales are declining, blames the one-size-fits-all theme products for gobbling up a greater slice of the market share. “Everybody is tired of these huge, monster multipurpose themes having the same price as normal themes, and that’s pretty much killing the marketplaces. But Envato couldn’t care less, as long as they get their share,” he said. In another thread, which ended up getting locked, there are 27 pages of comments from users speculating about why their sales have been dropping. Members cite seasonal buying fluctuations, piracy, Themeforest’s recent drop in Google search rankings, VAT and hidden price additions on checkout, and unfair pricing advantages for monster themes that claim to do everything, among other possible causes. In one thread, titled “More than 50% sales drop for most of the authors. Does TF care for Authors?“, an Envato community officer offered the following comment: We don’t really give sales updates over the forums other than to say your sales can go up and down for a multitude of reasons. Try not to assume the sky is falling every time the USA has a long weekend We have fast and slow periods throughout the year same as any business, and your portfolio will no doubt have peaks and valleys as well. This kind of generic reply has left theme authors scratching their heads, despite multiple threads in the forums popping up with concerns from those who are alarmed by the sudden drop. Many WordPress theme authors depend on Themeforest as their primary source of income. In one reply, the Aligator Studio seller sums up their concerns and frustration with the inability to convince Envato of the unusual circumstances that are affecting large numbers of sellers: We are not talking about valleys and peaks, we’re talking about a general traffic and sales fall, from New Year until now, especially after April. We’re not talking about regular ups and downs (sometimes steeper, sometimes not), due to longer weekends, summer holidays, and general and the usual stuff happening here in the last couple of years. It’s not a sky falling – it’s inability to pay our bills, we’re not fanatics that foresee the end of the world. Envato has yet to provide an official statement about the marketplace-wide decline in sales, apart from recognizing the network’s unavailability due to the recent DDoS attack. Source: http://wptavern.com/envato-targeted-by-ddos-attack-wordpress-theme-authors-report-major-decline-in-sales
View article:
Envato Targeted by DDoS Attack, WordPress Theme Authors Report Major Decline in Sales


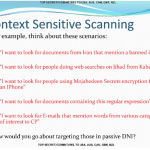 XKeyscore runs on Linux-based servers across 150 field sites scattered across the globe. No matter what you’ve done on the internet, you can bet the National Security Agency has a record of it. Newly released documents leaked by Edward Snowden shed light on the scale and scope of the XKeyscore program, a program described by one classified document as the “widest-reaching” system for gathering information from the internet. The new batch of documents detail one of the most extensive programs used in the US government’s arsenal on global surveillance, more than two years after it was first revealed by The Guardian . The program, which runs on hundreds of Red Hat Linux-based servers scattered around the globe (likely in US Embassy buildings), allows analysts to filter the vast amount of incidental data created when a user browses the web. The program allows analysts to selectively pick out usernames and passwords, browser history, emails sent and received, social media data, and even locations and detect whether or not a computer is vulnerable to certain kinds of malware or other threats. A single unique identifier, such as a username, password, email fragment, or even images, can be used to trace a person’s online activities with extreme precision. One of the documents said the program was successful in capturing 300 terrorists based on intelligence it had collected. Out of all the programs, XKeyscore may be the largest in scope, with some field sites sifting through more than 20 terabytes of data per day, according to The Intercept , collected from the various fiber cables around the world. The newly-released trove of documents details a broader scope of access to personal information that NSA analysts have. Those include: The NSA was able to acquire talking points UN Secretary General Ban Ki-moon wanted to bring up with US President Barack Obama through the Blarney program, which feeds the XKeyscore program. (Blarney is thought to be a program that taps fiber optic cables at core internet choke points around the US and the world.) When a group of people overload a server or network with a flood of network traffic (causing a “distributed denial-of-service” or DDoS attack), users can be identified using XKeyscore. One document boasts of how “criminals” can be found through the program. NSA analysts can plug in queries such as “show me all the exploitable machines in [whichever] country” and have returned to them a list of computers and devices that are vulnerable to the hacking exploits of the NSA’s elite intrusion unit, known as Tailored Access Operations (TAO). That also extends to “find all iPhones in Nigeria,” or “find Germans living in Pakistan.” One of the documents showing how NSA analysts can use XKeyscore Oversight of the program is limited at best. The system is littered with reminders not to breach human rights’ laws or minimization procedures designed to prevent Americans’ data from being used by the program. Yet, not everything is audited. System administrators often log in to the program under one username, “oper,” which is used across multiple people and divisions, making any actions carried out under that name almost impossible to track. XKeyscore can search other databases, like Nucleon, which “intercepts telephone calls and routes the spoken words” to a database. (So yes, the US government is listening to some people’s phone calls.) One newly-released document showed more than 8,000 people are ensnared by the program, with more than half-a-million voice files recorded each day. An al-Qaeda operative is said to have searched Google for his own name, among other aliases, which was picked up by the XKeyscore program, another document shows . The program is able to snoop inside documents attached to emails, one document says . That supposedly can help determine who had authored a Word or PowerPoint document. NSA has its own internal online newspaper, a document shows , which the agency dubs the “NSA Daily.” It’s a top secret publication, which only agents belonging to UK, US, Australian, Canadian, and New Zealand intelligence agencies can access. The NSA said in a statement (of which portions had been used in previous statements) that its foreign intelligence operations are “authorized by law” and are “subject to multiple layers of stringent internal and external oversight.” Source: http://www.zdnet.com/article/nsa-xkeyscore-spy-united-nations-target-denial-service-more/
XKeyscore runs on Linux-based servers across 150 field sites scattered across the globe. No matter what you’ve done on the internet, you can bet the National Security Agency has a record of it. Newly released documents leaked by Edward Snowden shed light on the scale and scope of the XKeyscore program, a program described by one classified document as the “widest-reaching” system for gathering information from the internet. The new batch of documents detail one of the most extensive programs used in the US government’s arsenal on global surveillance, more than two years after it was first revealed by The Guardian . The program, which runs on hundreds of Red Hat Linux-based servers scattered around the globe (likely in US Embassy buildings), allows analysts to filter the vast amount of incidental data created when a user browses the web. The program allows analysts to selectively pick out usernames and passwords, browser history, emails sent and received, social media data, and even locations and detect whether or not a computer is vulnerable to certain kinds of malware or other threats. A single unique identifier, such as a username, password, email fragment, or even images, can be used to trace a person’s online activities with extreme precision. One of the documents said the program was successful in capturing 300 terrorists based on intelligence it had collected. Out of all the programs, XKeyscore may be the largest in scope, with some field sites sifting through more than 20 terabytes of data per day, according to The Intercept , collected from the various fiber cables around the world. The newly-released trove of documents details a broader scope of access to personal information that NSA analysts have. Those include: The NSA was able to acquire talking points UN Secretary General Ban Ki-moon wanted to bring up with US President Barack Obama through the Blarney program, which feeds the XKeyscore program. (Blarney is thought to be a program that taps fiber optic cables at core internet choke points around the US and the world.) When a group of people overload a server or network with a flood of network traffic (causing a “distributed denial-of-service” or DDoS attack), users can be identified using XKeyscore. One document boasts of how “criminals” can be found through the program. NSA analysts can plug in queries such as “show me all the exploitable machines in [whichever] country” and have returned to them a list of computers and devices that are vulnerable to the hacking exploits of the NSA’s elite intrusion unit, known as Tailored Access Operations (TAO). That also extends to “find all iPhones in Nigeria,” or “find Germans living in Pakistan.” One of the documents showing how NSA analysts can use XKeyscore Oversight of the program is limited at best. The system is littered with reminders not to breach human rights’ laws or minimization procedures designed to prevent Americans’ data from being used by the program. Yet, not everything is audited. System administrators often log in to the program under one username, “oper,” which is used across multiple people and divisions, making any actions carried out under that name almost impossible to track. XKeyscore can search other databases, like Nucleon, which “intercepts telephone calls and routes the spoken words” to a database. (So yes, the US government is listening to some people’s phone calls.) One newly-released document showed more than 8,000 people are ensnared by the program, with more than half-a-million voice files recorded each day. An al-Qaeda operative is said to have searched Google for his own name, among other aliases, which was picked up by the XKeyscore program, another document shows . The program is able to snoop inside documents attached to emails, one document says . That supposedly can help determine who had authored a Word or PowerPoint document. NSA has its own internal online newspaper, a document shows , which the agency dubs the “NSA Daily.” It’s a top secret publication, which only agents belonging to UK, US, Australian, Canadian, and New Zealand intelligence agencies can access. The NSA said in a statement (of which portions had been used in previous statements) that its foreign intelligence operations are “authorized by law” and are “subject to multiple layers of stringent internal and external oversight.” Source: http://www.zdnet.com/article/nsa-xkeyscore-spy-united-nations-target-denial-service-more/