The collaborative coding site scrambled to withstand the opening salvo from what researchers dubbed China’s Great Cannon. But CEO Chris Wanstrath says that was just the beginning. To survive, startups must surmount challenges like product development, funding negotiations and cash flow. GitHub CEO Chris Wanstrath can add a very different challenge to his list: a sustained five-day network attack that some say marked the beginning of a new, more aggressive chapter in China’s relations with the outside computing world. GitHub’s business, founded in 2008, is all about letting programmers work together. It offers a place where individual coders can contribute to each other’s software projects, and where companies like Google, Facebook and Twitter can share work through the collaborative open-source movement. But on March 26, two organizations with GitHub accounts came under attack. Attacks on GitHub are common, though it can be nearly impossible to figure out their origins, Wanstrath said during an interview here at the company’s Merge conference. Even teenagers flexing their online muscles can launch an attack by buying access to a collection of machines. But this recent GitHub attack one was the worst in the company’s history. The company’s seven-person response team worked around the clock in a cat-and-mouse game to keep GitHub running even as the attackers shifted from one type of attack to another. Those two targeted GitHub sites were GreatFire.org, a nonprofit organization that tries to help people bypass Chinese censorship, and the Chinese New York Times, according to an analysis of the attack by network security software firm Netresec. But it hurt all of GitHub’s operations. That’s because it was a distributed denial-of-service (DDOS) attack, where countless computers around the world overwhelmed GitHub’s servers to the point where they couldn’t provide the online service they’re supposed to provide. Researchers dubbed the attack the Great Cannon. The Great Firewall of China has been around for years, letting the government block access to sites it doesn’t want its Chinese residents seeing, but the Great Cannon serves an offensive rather than defense purpose, the researchers at the University of Toronto, University of California and Princeton University wrote. When people visited innocent Web pages, the attacker’s servers would replace website code with malicious code that would direct their browsers to ceaselessly reload the GitHub pages. “The Cannon manipulates the traffic of bystander’ systems outside China, silently programming their browsers to create a massive DDOS attack,” the researchers said. The Chinese system could work similarly to one run by the US National Security Agency and its British counterpart, Government Communications Headquarters, according to documents leaked by former NSA contractor Edward Snowden. These programs, called Quantum and Foxacid, appeared to target the anonymous communication technology called Tor and employees at Belgian telecommunications company Belgacom, according to security expert Bruce Schneier and Der Spiegel, a German news publication. Wanstrath sat down with CNET’s Stephen Shankland to discuss the GitHub attack. The following is an edited transcript of their conversation. What was your first inkling that you were under attack? Wanstrath: A traffic spike. We started to get an unusual amount of traffic. It was coming from all over the world — were we on Oprah? Then we realized people’s phones or computers were getting hijacked to load GitHub. We saw the man-on-the-side attack. But that was just was the first attack of a series. Wanstrath: Yes. It was a mix of new stuff and boring stuff. The nature of the first attack was novel. After that we saw other attacks that were traditional, like SYN floods. In five days, we saw 18 or 20 attacks. How often are you attacked ordinarily? Wanstrath: Once a month, if not more. We’ve got monitoring. We have a good incident response program set up. When there’s an attack profile, you get paged. The main event of a DDOS is overwhelming the network with traffic. When you get a million requests and they’re exactly the same in one second, that’s a DDOS. We have automated systems, then an ops team on the network around the clock. So was somebody trying to send a message? Wanstrath: Of course. I just don’t know who the message was for. I’m not even sure the message is to us. You don’t need to be a state government to run this sort of attack. Sometimes it’s teenagers fighting over message boards. If it was from China, is there an easier way to target GreatFire and the New York Times than launching a five-day attack? Wanstrath: Sure. That’s why it’s confusing to conclude it came from China. In China, the New York Times is blocked, the Wall Street Journal is blocked. China blocks [lots] of websites. And after five days they chose to disengage? Did you vanquish the enemy? Wanstrath: It was an ongoing battle. We successfully mitigated some of their attacks. Even though we were winning, we were fighting the whole time. There was a lot of press about it, which may have contributed to the disengagement. What’s frustrating is there was no ransom note — no request for anything. Just an attack. What did it do to your business? Wanstrath: The outages are frustrating. We never went totally down, but people had errors. It interrupted people’s workflows. At GitHub, people were up all weekend. So is this a badge of honor? A sign that you’ve arrived? Wanstrath: It’s hard to feel that way when there are real people trying to do real work with GitHub. If this is what arriving is like, this isn’t what we signed up for. We’ve been attacked for awhile. We have defenses. But GitHub two or three years ago would not have successfully mitigated this attack. You can imagine a smaller company just falling over. What did you learn? Have you changed any technology or policies? Wanstrath: We learned a lot on a technical level. The DDOS is such a cat-and-mouse game. We can’t share broadly with the technology community to say here’s how to protect yourselves, though. It’s like bacteria. If the attackers know what we do, then they’ll stop doing that attack. Now, they don’t know what we know. Did you talk to the US government about the attack? Wanstrath: We can’t say it really has a China component because we can’t prove anything. We can’t really ask for help for anyone. I’m not sure what would have happened if this had lasted a month. Source: http://www.cnet.com/au/news/how-startup-github-survived-a-massive-five-day-network-attack-q-a/
Original post:
How startup GitHub survived a massive five-day DDoS attack

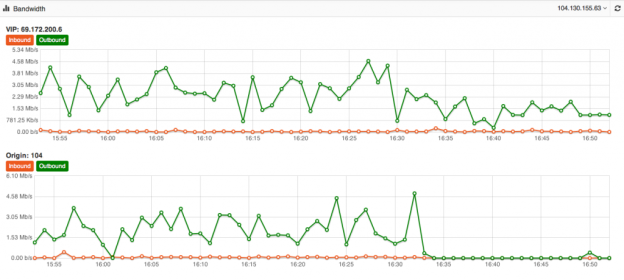
 Its one of the biggest mysteries to me I have seen in my 15+ years of Internet hosting and cloud based services. The mystery is, why do people use a Content Delivery Network for their website yet never fully optimize their site to take advantage of the speed and volume capabilities of the CDN. Just because you use a CDN doesn’t mean your site is automatically faster or even able to take advantage of its ability to dish out mass amounts of content in the blink of an eye. At DOSarrest I have seen the same mystery continue, this is why I have put together this piece on using a CDN and hopefully help those who wish to take full advantage of a CDN. Most of this information is general and can be applied to using any CDN but I’ll also throw in some specifics that relate to DOSarrest. Some common misconceptions about using a CDN As soon as I’m configured to use a CDN my site will be faster and be able to handle a large amount of web visitors on demand. Website developers create websites that are already optimized and a CDN won’t really change much. There’s really nothing I can do to make my website run faster once its on a CDN. All CDN’s are pretty much the same. Here’s what I have to say about the misconceptions noted above In most cases the answer to this is…. NO !! If the CDN is not caching your content your site won’t be faster, in fact it will probably be a little slower, as every request will have to go from the visitor to the CDN which will in turn go and fetch it from your server then turn around and send the response back to the visitor. In my opinion and experience website developers in general do not optimize websites to use a CDN. In fact most websites don’t even take full advantage of a browsers’ caching capability. As the Internet has become ubiquitously faster, this fine art has been left by the wayside in most cases. Another reason I think this has happened is that websites are huge, complex and a lot of content is dynamically generated coupled with very fast servers with large amounts of memory. Why spend time on optimizing caching, when a fast server will overcome this overhead. Oh yes you can and that’s why I have written this piece…see below No they aren’t. Many CDN’s don’t want you know how things are really working from every node that they are broadcasting your content from. You have to go out and subscribe to a third party service, if you have to get a third party service, do it, it can be fairly expensive but well worth it. How else will you know how your site is performing from other geographic regions. A good CDN should let you know the following in real-time but many don’t. Number of connections/requests between the CDN and Visitors. Number of connections/requests between the CDN and your server (origin). You want try and have the number of requests to your server to be less than the number of requests from the CDN to your visitors. *Tip- Use HTTP 1.1 on both “a” & “b” above and try and extend the keep-alive time on the origin to CDN side Bandwidth between the CDN and Internet visitors Bandwidth between the CDN and your server (origin) *Tip – If bandwidth of “c” and “d” are about the same, news flash…You can make things better. Cache status of your content (how many requests are being served by the CDN) *Tip – This is the best metric to really know if you are using your CDN properly. Performance metrics from outside of the CDN but in the same geographic region *Tip- Once you have the performance metrics from several different geographic regions you can compare the differences once you are on a CDN, your site should load faster the further away the region is located from your origin server, if you’re caching properly. For the record DOSarrest provides all of the above in real-time and it’s these tools I’ll use to explain on how to take full advantage of any CDN but without any metrics there’s no scientific way to know you’re on the right track to making your site super fast. There are five main groups of cache control tags that will effect how and what is cached. Expires : When attempting to retrieve a resource a browser will usually check to see if it already has a copy available for reuse. If the expires date has past the browser will download the resource again. Cache-control : HTTP 1.1 this expands on the functionality offered by Expires. There are several options available for the cache control header: – Public : This resource is cacheable. In the absence of any contradicting directive this is assumed. – Private : This resource is cachable by the end user only. All intermediate caching devices will treat this resource as no-cache. – No-cache : Do not cache this resource. – No-store : Do not cache, Do not store the request, I was never here – we never spoke. Capiche? – Must-revalidate : Do not use stale copies of this resource. – Proxy-revalidate : The end user may use stale copies, but intermediate caches must revalidate. – Max-age : The length of time (in seconds) before a resource is considered stale. A response may include any combination of these headers, for example: private, max-age=3600, must-revalidate. X-Accel-Expires : This functions just like the Expires header, but is only intended for proxy services. This header is intended to be ignored by browsers, and when the response traverses a proxy this header should be stripped out. Set-Cookie : While not explicitly specifying a cache directive, cookies are generally designed to hold user and/or session specific information. Caching such resources would have a negative impact on the desired site functionality. Vary : Lists the headers that should determine distinct copies of the resource. Cache will need to keep a separate copy of this resource for each distinct set of values in the headers indicated by Vary. A Vary response of “ * “ indicates that each request is unique. Given that most websites in my opinion are not fully taking advantage of caching by a browser or a CDN, if you’re using one, there is still a way around this without reviewing and adjusting every cache control header on your website. Any CDN worth its cost as well as any cloud based DDoS protection services company should be able to override most website cache-control headers. For demonstration purposes we used our own live website DOSarrest.com and ran a traffic generator so as to stress the server a little along with our regular visitor traffic. This demonstration shows what’s going on, when passing through a CDN with respect to activity between the CDN and the Internet visitor and the CDN and the customers server on the back-end. At approximately 16:30 we enabled a feature on DOSarrest’s service we call “Forced Caching” What this does is override in other words ignore some of the origin servers cache control headers. These are the results: Notice that bandwidth between the CDN and the origin (second graph) have fallen by over 90%, this saves resources on the origin server and makes things faster for the visitor. This is the best graphic illustration to let you know that you’re on the right track. Cache hits go way up, not cached go down and Expired and misses are negligible. The graph below shows that the requests to the origin have dropped by 90% ,its telling you the CDN is doing the heavy lifting. Last but not least this is the fruit of your labor as seen by 8 sensors in 4 geographic regions from our Customer “ DEMS “ portal. The site is running 10 times faster in every location even under load !
Its one of the biggest mysteries to me I have seen in my 15+ years of Internet hosting and cloud based services. The mystery is, why do people use a Content Delivery Network for their website yet never fully optimize their site to take advantage of the speed and volume capabilities of the CDN. Just because you use a CDN doesn’t mean your site is automatically faster or even able to take advantage of its ability to dish out mass amounts of content in the blink of an eye. At DOSarrest I have seen the same mystery continue, this is why I have put together this piece on using a CDN and hopefully help those who wish to take full advantage of a CDN. Most of this information is general and can be applied to using any CDN but I’ll also throw in some specifics that relate to DOSarrest. Some common misconceptions about using a CDN As soon as I’m configured to use a CDN my site will be faster and be able to handle a large amount of web visitors on demand. Website developers create websites that are already optimized and a CDN won’t really change much. There’s really nothing I can do to make my website run faster once its on a CDN. All CDN’s are pretty much the same. Here’s what I have to say about the misconceptions noted above In most cases the answer to this is…. NO !! If the CDN is not caching your content your site won’t be faster, in fact it will probably be a little slower, as every request will have to go from the visitor to the CDN which will in turn go and fetch it from your server then turn around and send the response back to the visitor. In my opinion and experience website developers in general do not optimize websites to use a CDN. In fact most websites don’t even take full advantage of a browsers’ caching capability. As the Internet has become ubiquitously faster, this fine art has been left by the wayside in most cases. Another reason I think this has happened is that websites are huge, complex and a lot of content is dynamically generated coupled with very fast servers with large amounts of memory. Why spend time on optimizing caching, when a fast server will overcome this overhead. Oh yes you can and that’s why I have written this piece…see below No they aren’t. Many CDN’s don’t want you know how things are really working from every node that they are broadcasting your content from. You have to go out and subscribe to a third party service, if you have to get a third party service, do it, it can be fairly expensive but well worth it. How else will you know how your site is performing from other geographic regions. A good CDN should let you know the following in real-time but many don’t. Number of connections/requests between the CDN and Visitors. Number of connections/requests between the CDN and your server (origin). You want try and have the number of requests to your server to be less than the number of requests from the CDN to your visitors. *Tip- Use HTTP 1.1 on both “a” & “b” above and try and extend the keep-alive time on the origin to CDN side Bandwidth between the CDN and Internet visitors Bandwidth between the CDN and your server (origin) *Tip – If bandwidth of “c” and “d” are about the same, news flash…You can make things better. Cache status of your content (how many requests are being served by the CDN) *Tip – This is the best metric to really know if you are using your CDN properly. Performance metrics from outside of the CDN but in the same geographic region *Tip- Once you have the performance metrics from several different geographic regions you can compare the differences once you are on a CDN, your site should load faster the further away the region is located from your origin server, if you’re caching properly. For the record DOSarrest provides all of the above in real-time and it’s these tools I’ll use to explain on how to take full advantage of any CDN but without any metrics there’s no scientific way to know you’re on the right track to making your site super fast. There are five main groups of cache control tags that will effect how and what is cached. Expires : When attempting to retrieve a resource a browser will usually check to see if it already has a copy available for reuse. If the expires date has past the browser will download the resource again. Cache-control : HTTP 1.1 this expands on the functionality offered by Expires. There are several options available for the cache control header: – Public : This resource is cacheable. In the absence of any contradicting directive this is assumed. – Private : This resource is cachable by the end user only. All intermediate caching devices will treat this resource as no-cache. – No-cache : Do not cache this resource. – No-store : Do not cache, Do not store the request, I was never here – we never spoke. Capiche? – Must-revalidate : Do not use stale copies of this resource. – Proxy-revalidate : The end user may use stale copies, but intermediate caches must revalidate. – Max-age : The length of time (in seconds) before a resource is considered stale. A response may include any combination of these headers, for example: private, max-age=3600, must-revalidate. X-Accel-Expires : This functions just like the Expires header, but is only intended for proxy services. This header is intended to be ignored by browsers, and when the response traverses a proxy this header should be stripped out. Set-Cookie : While not explicitly specifying a cache directive, cookies are generally designed to hold user and/or session specific information. Caching such resources would have a negative impact on the desired site functionality. Vary : Lists the headers that should determine distinct copies of the resource. Cache will need to keep a separate copy of this resource for each distinct set of values in the headers indicated by Vary. A Vary response of “ * “ indicates that each request is unique. Given that most websites in my opinion are not fully taking advantage of caching by a browser or a CDN, if you’re using one, there is still a way around this without reviewing and adjusting every cache control header on your website. Any CDN worth its cost as well as any cloud based DDoS protection services company should be able to override most website cache-control headers. For demonstration purposes we used our own live website DOSarrest.com and ran a traffic generator so as to stress the server a little along with our regular visitor traffic. This demonstration shows what’s going on, when passing through a CDN with respect to activity between the CDN and the Internet visitor and the CDN and the customers server on the back-end. At approximately 16:30 we enabled a feature on DOSarrest’s service we call “Forced Caching” What this does is override in other words ignore some of the origin servers cache control headers. These are the results: Notice that bandwidth between the CDN and the origin (second graph) have fallen by over 90%, this saves resources on the origin server and makes things faster for the visitor. This is the best graphic illustration to let you know that you’re on the right track. Cache hits go way up, not cached go down and Expired and misses are negligible. The graph below shows that the requests to the origin have dropped by 90% ,its telling you the CDN is doing the heavy lifting. Last but not least this is the fruit of your labor as seen by 8 sensors in 4 geographic regions from our Customer “ DEMS “ portal. The site is running 10 times faster in every location even under load !