Leaders at four security technology companies say the distributed-denial-of-service attacks that have hit 10 U.S. banks in recent weeks highlight the need for new approaches to preventing and responding to online outages. “Attackers have broadened their toolkits, and DDoS is a not just a blunt instrument anymore,” says Jason Malo , a fraud analyst CEB TowerGroup and former DDoS-prevention expert for domain-naming-system registry operator VeriSign. These experts advise banking institutions to: Use appropriate technology, including cloud-based Web servers, which can handle overflow, when high volumes of Web traffic strike; Assess ongoing DDoS risks, such as through tests that mimic real-world attacks; Implement online outage mitigation and response strategies before attacks hit; Train staff to recognize the signs of a DDoS attack. During a DDoS attack, a website is flooded with what security experts often call “junk” traffic – a saturation of requests that overwhelm the site’s servers, preventing them from being able to respond to legitimate traffic. In essence, DDoS attacks take websites down because the servers can’t handle the traffic. Security experts interviewed for this story say most banks have failed to address this vulnerability to high volumes of traffic. DDoS: Banks on Alert Starting in mid-September, DDoS attacks have resulted in online outages at 10 major U.S. banks . The hacktivist group Izz ad-Din al-Qassam Cyber Fighters has taken credit for the hits, saying the attacks are motivated by outrage related to a YouTube movie trailer deemed offensive to Muslims. But security experts say DDoS attacks are often used as tools of distraction to mask fraud in the background (see DDoS Attacks: First Signs of Fraud? ). To reduce their risk of DDoS takedown, experts say banks need to address three key areas: Layered user authentication at login, which consumes bandwidth; Reliance on Internet service providers not equipped to handle extreme bandwidth demands; and The internal management of Web servers, which limits banks’ ability to hand off traffic overflow when volumes are excessive. Expert Advice Fraud should always be an institution’s top concern, meaning addressing DDoS threats should be a priority, experts say. “DDoS protections have quickly become a new industry best practice,” Malo says. But DDoS attacks pose unique challenges for banks and credit unions. The additional layers of security institutions already implement, such as enhanced user authentication, transaction verification and device identification , demand more bandwidth. So when a bank is hit by a DDoS attack, bandwidth is strained more than it would be at a non-banking e-commerce site, says Mike Smith, a senior security evangelist at Akamai Technologies, which specializes in Internet traffic monitoring and cloud-based DDoS protections (see New Bank Attacks Expected Today? ). So what protections make sense? BankInfoSecurity asked security vendors VeriSign, Prolexic, Cisco and Akamai Technologies for their top recommendations. They all stressed that no one-size-fits-all approach to thwarting attacks exists. Nevertheless, they identified several best practices. Use Appropriate Technology When it comes to selecting the right technologies to minimize DDoS-related outages, vendors advise: Rely on the cloud. No internal server could be expected to handle the amount of traffic these recent DDoS attacks have pushed. Akamai’s Smith says the average amount of traffic coming in during some of those individual attacks equaled about 65 gigabytes per second. “Even at the height of the Anonymous attacks, we saw traffic coming in from 7,000 or 8,000 people [at approximately 1 gigabyte per second],” he says. By relying on cloud-based servers and systems, banks can expand their bandwidth. “It’s never a good idea to manage everything internally,” says Joe Dallatore, senior manager of the Cisco Security & Research Information Group, which specializes in security threat monitoring and online event tracking. Working with a cloud vendor also can help institutions more readily identify a DNS-server attack or other DDoS attack, Dallatore says. Using DNS providers with the capacity to absorb an attack makes sense, because when DNS fails, all other services fail, says Akamai’s Smith. “This is why almost all the large banks use a DNS provider in some capacity, and it’s a proactive defense that is always turned on by default,” he adds. Use virtual private networks. VPNs indirectly improve DDoS protections, says Matt Wilson, who oversees strategic technologies at VeriSign. Attackers target publicly available sites because they are public. But a VPN cannot protect an entire infrastructure. For complete protection, banks and businesses must continue to rely on other technologies for firewall management as well as server and router maintenance, he says. A better solution, Akamai’s Smith suggests, is VPN over MPLS [multiprotocol label switching] for critical or business-to-business functions. Apply challenge-and-response. Malo says banks should encourage vendors to develop DDoS protections that “challenge” traffic. These protections, he says, could mirror challenge-and-response options, such as CAPTCHA images, used for online banking. A CAPTCHA image uses distorted letters or numbers that an online user is required to enter at login to help affirm authenticity. “DDoS mitigation is not just about finding a signature and putting mechanisms in to filter or block traffic,” Malo says. “Mitigation also includes introducing challenge-response.” Challenge-and-response options would help banking institutions differentiate legitimate traffic from so-called junk traffic often associated with DDoS attacks, he adds. But Akamai’s Smith warns that challenge-and-response during a large DDoS attack could be dangerous, since challenge-and-response takes one request and turns it into four. “This does not scale, and it sets you up for additional points of failure.” he says. For smaller attacks, challenge-and-response can be effective, however, “where we are worried about denying legitimate users because of mega-proxies, corporate Internet access points,” Smith says. Don’t rely on intrusion detection. Intrusion prevention and detection systems can be effective at picking up on anomalous traffic or behavior associated with a DDoS attack, CEB TowerGroup’s Malo says. But that’s not what those systems were primarily designed to do. While leaning on those systems can help DDoS detection, and in some cases help institutions thwart online outages, redirecting IPS and IDS can create new vulnerabilities. “When protection systems are redirected, banking institutions inadvertently create new vulnerabilities,” he says, because other defenses are weakened. Scrub. Traffic scrubbing, which clears suspected botnets and junk traffic at the ISP, can be effective, Cisco’s Dallatore says. The more bad traffic an institution can block at the outset, the better its chances of limiting an outage. Assess DDoS Risks Vendors stress that regularly assessing DDoS risks, such as through tests that mimic real-world attacks, is essential. “Run periodic table-top exercises to model how an attack could hit and then test the accompanying remediation strategies you’ve put in place,” says Stuart Scholly, president of Prolexic, which specializes in cloud-based services for website restoration after a DDoS attack. To set the stage for remediation plans and testing, vendors recommend banking institutions first: Know typical traffic patterns. To better assess risk, financial institutions must carefully determine what typical site traffic looks like, Malo says. That way, when a DDoS attack hits, atypical traffic patterns are more obvious. Understand the infrastructure. Understand the Web applications, online bandwidth limits and any infrastructure elements that could affect site capacity. Akamai’s Smith says network segmentation can limit the impact an attack has on other services inside the same infrastructure. “At a minimum, critical sites should be provisioned onto their own, dedicated network circuits and border devices to limit the impact of both an attack against them and from attacks against other services in the same data center,” he says. “Brochureware sites,” consumer transactional sites and business sites are good candidates to break out into their own infrastructure, Smith says, while redirect, typo and marketing-campaign sites can be run from shared infrastructure. Mitigation and Response DDoS mitigation strategies and response plans should be included in disaster recovery and business continuity strategies, Prolexic’s Scholly says. Those strategies also must include definitive communication and action plans, Cisco’s Dallatore says. Communicating with employees and the public soon after a DDoS attack is critical for reputational preservation. “You want to be sure operational people, for instance, can reach the decision makers or have the authority to make decisions when a site goes down,” Dallatore says. During the recent wave of attacks, banks’ communication with the public varied. Some institutions acknowledged their sites went down because of DDoS attacks, while others only said their sites experienced intermittent outages. Greg Nowak of the Information Security Forum says most institutions have been too quiet – fueling the public’s fears about the outages. “They seem to be regarding it as a secret,” Nowak says. “[The banks] should be taking the opportunity to explain to their customers the difference between a denial-of-service attack and some sort of hacking attack that actually puts information at risk.” Provide Training Training staff to recognize the signs of an attack is essential, vendors advise. Bank and credit union employees must understand what DDoS attack traffic patterns look like, says Prolexic’s Scholly. Front-line staff members also need to know how to respond if they start getting calls about a site being down. BITS , the technology division of the Financial Services Roundtable, says banks and credit unions need to clearly communicate with customers and members that their financial information and accounts are secure. Among BITS recommendations: Explain that attacks have not resulted in unauthorized access to customer information; Reiterate to consumers that banking institutions use sophisticated online security strategies to protect customer accounts; Let consumers know that institutions continue to invest in technology to defend against potential attacks. “We want the public to know that institutions are taking steps to address these attacks – with ISPs and other security providers – and there is a fair amount of collaboration going on with regulators and the Department of Homeland Security about the threats and how to address them,” says John Carlson, executive vice president of BITS. “You can’t underestimate the importance of training, and the role it plays in your business continuity planning,” Scholly says. “When you are prepared, it makes a world of difference.” Source: http://www.bankinfosecurity.com/what-to-do-about-ddos-attacks-a-5271/p-3
View article:
What to Do About Distributed Denial of Service ‘DDoS’ attack

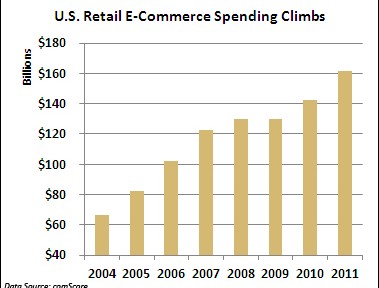
 A string of cyber attacks on U.S. financial institutions has created headaches this fall by slowing down or preventing online banking access for millions of Americans. But imagine the real economic damage that similar-style attacks would cause if they struck U.S. retailers this holiday-shopping season, potentially eating into projected online sales of $54 billion. While retailers deserve credit for bolstering their defenses against credit-card-hungry organized crime rings, security professionals believe the industry is vulnerable to this different kind of onslaught aimed at crippling online sales. “The gloves are off in cyber space. The reality is if they want it to get worse, it can get worse,” said Dave Aitel, a former computer scientist at the National Security Agency. “I don’t think people are really prepared mentally to what happens if Amazon goes down.” Unlike the ongoing cyber attacks against U.S. banks, there doesn’t appear to be a specific cyber threat against retailers. Yet there are concerns that retailers aren’t ready for denial-of-service (DDoS) attacks from a powerful state actor like Iran, which many in the U.S. government suspect had a hand in the recent attacks on financial institutions like Bank of America (BAC) and J.P. Morgan Chase (JPM). “The Iranians are in the business of making a point and the bank attacks are not likely to have the impact they need, hence retailers are the next most likely target, especially in the holiday season,” said Aitel, CEO of Immunity, a cyber security firm that works with Fortune 500 companies. Online Sales Exceed $160B It’s hard to overstate the importance of e-commerce in today’s smartphone and social network dominated world. According to comScore (CSOR), annual U.S. retail e-commerce spending has surged 143% since 2004 to $161.52 billion last year. Despite the sluggish domestic economy and tepid retail sales growth, e-commerce spending jumped 13% between 2010 and 2011. Online shopping is crucial during the all-important holiday-shopping season. E-commerce spending rose 14% last holiday season to $37.2 billion, comScore said. In the face of continued economic uncertainty, online spending is projected to climb 17% this season to $54.47 billion, according to MarketLive. “It’s very important for any retailer to have a web presence or you risk being left out in the cold,” said Andrew Lipsman, vice president of industry analysis at comScore, who noted that even in-person purchases typically originate online. Adapting to Shifting Threat Security professionals believe retailers’ cyber defenses are more porous than those of financial institutions — and even some banks succumbed to relentless DDoS attacks this fall. Given their prior experience combating thieves in Russia and elsewhere trying to siphon funds or snatch credit-card numbers, retailers aren’t really positioned to halt massive DDoS attacks from powerful state actors like Iran. “That’s a very different threat and in many ways is more severe,” said Aitel. “They’re not thinking: What if it’s not about the money? What if someone wants to take me out just to take me out?” Cedric Leighton, a former NSA official, said he agrees that retailers are not as well prepared as their financial peers. “I don’t think they’ve gotten to the point where they can truly say their whole cyber supply chain is as well secured as they need to be in this day and age,” said Leighton, CEO of a Washington, D.C.-based risk-management consultancy. Leighton said hackers could also disrupt companies’ supply chains by messing with order quantities and locations, creating costly problems for retailers. Just this week Barnes & Noble (BKS) fell victim to a very sophisticated criminal attack that may have resulted in stolen credit and debit card information at 63 of its stores. Amazon Atop Target List The importance of a robust cyber defense is even more important for online retailers like Amazon.com and Overstock (OSTK). “If they aren’t available online, there is no business. They don’t exist,” said Ronen Kenig, director of security product marketing at Tel Aviv-based security firm Radware (RDWR). In a potential cyber attack on U.S. retailers, Amazon.com would clearly be the biggest prize. The Seattle company generated $17.4 billion in revenue last holiday quarter. “When you attack the United States you don’t attack Topeka, Kansas,” said Aitel. “Amazon is the big boy on the block. They are of course also the best protected.” Amazon.com and Wal-Mart (WMT) declined to comment for this story, while Target (TGT) didn’t respond to a request for comment. “Every company is going to look at what its exposure is. The greater the company is placed at risk, then the more they are going to invest in trying to protect themselves,” said Mallory Duncan, general counsel at the National Retail Federation. Noting that some companies “rely extremely heavily on the Internet,” Duncan said, “When you have a bet-the-company type of situation, they’re going to take extraordinary steps to protect that channel.” Cyber Monday in Focus Aitel suggested the days around Cyber Monday — the first work day after Black Friday — as a time when retailers need to be particularly vigilant about the cyber threat. According to comScore, U.S. e-commerce spending on Cyber Monday rose 22% last year to $1.25 billion, making it the highest online spending day in history. “The attackers always like to choose the worst time for the victim,” said Kenig. Bolstering Cyber Defenses So what specifically should retailers be doing to prevent or mitigate the impact of DDoS attacks this holiday season? Leighton said it’s crucial for companies to implement redundant systems with backups that allow switching from one system to the other when necessary. From a bigger picture standpoint, retailers should strive to install security programs that go above and beyond industry security standards, which Aitel said “are really the bottom bar.” Security professionals have been particularly alarmed by some recent cyber attacks that inflicted damage on physical assets, including a devastating attack unleashed on Saudi Arabia’s state run oil company Saudi Aramco Some believe Iran may have been behind this attack, which destroyed an estimated 30,000 computers. Aitel said, “Companies have to look at what happened to Saudi Aramco and say: What would we do if that happened to us? Until they have a good answer for that, they shouldn’t be sleeping that well.” For advanced DDoS protection against your eCommerce site click here . Source: http://www.foxbusiness.com/industries/2012/10/24/would-cyber-attacks-ruin-christmas-for-retailers/
A string of cyber attacks on U.S. financial institutions has created headaches this fall by slowing down or preventing online banking access for millions of Americans. But imagine the real economic damage that similar-style attacks would cause if they struck U.S. retailers this holiday-shopping season, potentially eating into projected online sales of $54 billion. While retailers deserve credit for bolstering their defenses against credit-card-hungry organized crime rings, security professionals believe the industry is vulnerable to this different kind of onslaught aimed at crippling online sales. “The gloves are off in cyber space. The reality is if they want it to get worse, it can get worse,” said Dave Aitel, a former computer scientist at the National Security Agency. “I don’t think people are really prepared mentally to what happens if Amazon goes down.” Unlike the ongoing cyber attacks against U.S. banks, there doesn’t appear to be a specific cyber threat against retailers. Yet there are concerns that retailers aren’t ready for denial-of-service (DDoS) attacks from a powerful state actor like Iran, which many in the U.S. government suspect had a hand in the recent attacks on financial institutions like Bank of America (BAC) and J.P. Morgan Chase (JPM). “The Iranians are in the business of making a point and the bank attacks are not likely to have the impact they need, hence retailers are the next most likely target, especially in the holiday season,” said Aitel, CEO of Immunity, a cyber security firm that works with Fortune 500 companies. Online Sales Exceed $160B It’s hard to overstate the importance of e-commerce in today’s smartphone and social network dominated world. According to comScore (CSOR), annual U.S. retail e-commerce spending has surged 143% since 2004 to $161.52 billion last year. Despite the sluggish domestic economy and tepid retail sales growth, e-commerce spending jumped 13% between 2010 and 2011. Online shopping is crucial during the all-important holiday-shopping season. E-commerce spending rose 14% last holiday season to $37.2 billion, comScore said. In the face of continued economic uncertainty, online spending is projected to climb 17% this season to $54.47 billion, according to MarketLive. “It’s very important for any retailer to have a web presence or you risk being left out in the cold,” said Andrew Lipsman, vice president of industry analysis at comScore, who noted that even in-person purchases typically originate online. Adapting to Shifting Threat Security professionals believe retailers’ cyber defenses are more porous than those of financial institutions — and even some banks succumbed to relentless DDoS attacks this fall. Given their prior experience combating thieves in Russia and elsewhere trying to siphon funds or snatch credit-card numbers, retailers aren’t really positioned to halt massive DDoS attacks from powerful state actors like Iran. “That’s a very different threat and in many ways is more severe,” said Aitel. “They’re not thinking: What if it’s not about the money? What if someone wants to take me out just to take me out?” Cedric Leighton, a former NSA official, said he agrees that retailers are not as well prepared as their financial peers. “I don’t think they’ve gotten to the point where they can truly say their whole cyber supply chain is as well secured as they need to be in this day and age,” said Leighton, CEO of a Washington, D.C.-based risk-management consultancy. Leighton said hackers could also disrupt companies’ supply chains by messing with order quantities and locations, creating costly problems for retailers. Just this week Barnes & Noble (BKS) fell victim to a very sophisticated criminal attack that may have resulted in stolen credit and debit card information at 63 of its stores. Amazon Atop Target List The importance of a robust cyber defense is even more important for online retailers like Amazon.com and Overstock (OSTK). “If they aren’t available online, there is no business. They don’t exist,” said Ronen Kenig, director of security product marketing at Tel Aviv-based security firm Radware (RDWR). In a potential cyber attack on U.S. retailers, Amazon.com would clearly be the biggest prize. The Seattle company generated $17.4 billion in revenue last holiday quarter. “When you attack the United States you don’t attack Topeka, Kansas,” said Aitel. “Amazon is the big boy on the block. They are of course also the best protected.” Amazon.com and Wal-Mart (WMT) declined to comment for this story, while Target (TGT) didn’t respond to a request for comment. “Every company is going to look at what its exposure is. The greater the company is placed at risk, then the more they are going to invest in trying to protect themselves,” said Mallory Duncan, general counsel at the National Retail Federation. Noting that some companies “rely extremely heavily on the Internet,” Duncan said, “When you have a bet-the-company type of situation, they’re going to take extraordinary steps to protect that channel.” Cyber Monday in Focus Aitel suggested the days around Cyber Monday — the first work day after Black Friday — as a time when retailers need to be particularly vigilant about the cyber threat. According to comScore, U.S. e-commerce spending on Cyber Monday rose 22% last year to $1.25 billion, making it the highest online spending day in history. “The attackers always like to choose the worst time for the victim,” said Kenig. Bolstering Cyber Defenses So what specifically should retailers be doing to prevent or mitigate the impact of DDoS attacks this holiday season? Leighton said it’s crucial for companies to implement redundant systems with backups that allow switching from one system to the other when necessary. From a bigger picture standpoint, retailers should strive to install security programs that go above and beyond industry security standards, which Aitel said “are really the bottom bar.” Security professionals have been particularly alarmed by some recent cyber attacks that inflicted damage on physical assets, including a devastating attack unleashed on Saudi Arabia’s state run oil company Saudi Aramco Some believe Iran may have been behind this attack, which destroyed an estimated 30,000 computers. Aitel said, “Companies have to look at what happened to Saudi Aramco and say: What would we do if that happened to us? Until they have a good answer for that, they shouldn’t be sleeping that well.” For advanced DDoS protection against your eCommerce site click here . Source: http://www.foxbusiness.com/industries/2012/10/24/would-cyber-attacks-ruin-christmas-for-retailers/