A new multimedia ballet, “HackPolitik,” fuses jarring, angular movements with electroacoustic music and video projection to interpret the activities of hacker collective Anonymous. Hacker collective Anonymous is going to the ballet. Take that in; it’s not often you’ll see Anonymous and ballet in the same sentence. The unusual pairing will take place November 15 and 16 at the Boston University Dance Theater, where the Juventas New Music Ensemble debuts “HackPolitik,” a new contemporary ballet based on the hacktivist group’s activities and personalities. The piece combines electroacoustic music, modern dance, and video projection to examine how the Internet impacts 21st century discourse and sometimes blurs the lines between activism and anarchy. Instead of pastel tutus, expect to see dancers in black and white, with dramatic face paint that evokes Guy Fawkes masks. And erratic, sometimes militant movements instead of fluid pirouettes. How do hacks on Twitter and LinkedIn accounts translate to physical movement? Neither the dance nor the music is neatly representative of things like Web site defacements, distributed denial-of-service attacks, and data theft, though they do aim to capture the mood of cyber insurgency. One scene, for example, opens with a soloist appearing to search for a way into something. Once she’s successful, the rest of the dancers join her with a series of advancing movements directed at one point in space that’s meant to represent the entity being attacked. “The movement interprets the initial culture of Anonymous as a crass, chaotic, and immature world out of which particular personalities and goals emerge,” choreographer Kate Ladenheim tells CNET. “For example, in the opening of the piece, we created a phrase that we lovingly refer to as the ‘f*@% you’ phrase. There are 10 examples of immature gestures/f*@%-you hand motions that are abstracted to become full bodied and then traveled through space in various ways.” This was Ladenheim’s take on trolling, memes, and the “all-around chaos of IRC and online message boards like 4chan.” The idea for “HackPolitik” came to Boston-based composer Peter Van Zandt Lane in late 2011, when some of Anonymous’ more high-profile politically driven cyberattacks grabbed the spotlight. Lane teaches a course at Brandeis University called “Protest and Propaganda in Music,” but hadn’t had much occasion to meld those interests with his creative work. “The idea of a ballet based on the global hacktivist movement excited me, as it was a way I could potentially pull these three spheres together,” he tells CNET. The two-act piece touches, among other things, on the December 2010 distributed denial-of-service attack on PayPal. It was organized in response to PayPal halting donations to the online leaked-documents clearinghouse WikiLeaks. Another of the ballet’s 10 scenes references Anonymous’ 2011 attack on HBGary Federal, a security firm trying to investigate the loosely organized global group. “The music, on its own, says…disorder, absurdity, cohesion/collaboration, militaristic triumph, humiliation, betrayal, etc.,” Lane says. “Choreography can connect these expressions a bit more concretely to the activities of Anonymous, but ultimately, the audience has to make connections themselves, between a generally abstract art form and the specific events that inspired them.” To create the ballet, Lane; Ladenheim, artistic director of NY-based contemporary dance company The People Movers; and conductor Lidiya Yankovskaya, artistic director of the Juventas New Music Ensemble, mined author Parmy Olson’s writings on Anonymous, which closely examine the global activist movement. Anonymous has supporters worldwide, as evidenced by this week’s “Million Mask March” in cities from Washington, D.C., to Tokyo to Sao Paulo, Brazil. Some pioneers of the hacktivist movement, however, have criticized Anonymous, saying its methods abridge free speech and hurt the cause . But “HackPolitik,” Lane insists, isn’t about taking sides. “For me,” he says, “the piece is less about answers, and more about bringing up questions on how we emotionally and artistically are able to respond to the influence of technology on our society.” Source: http://news.cnet.com/8301-17938_105-57611236-1/ddos-as-dance-anonymous-hits-the-ballet/
Taken from:
DDoS as dance: Anonymous hits the ballet


 Much has been discussed about the damage that the Advanced Persistent Threat (APT) attacks cause to corporates and governments alike. It is estimate that at least 50% of Fortune 500 companies have been compromised by APT, and the potential financial damage to these organizations is almost impossible to quantify, but probably in the trillions of US dollars. Compared to this a crude Denial of Service (DoS) attack or its more advance siblings, the Distributed Denial of Service (DDoS) attacks and Distributed Reflector (DRDoS) attacks, their outcome seems pretty benign- your site is being bombarded by thousands of request for information, until the server gives up and no-one can actually use the site. Once the attack stops, access is possible again and no damage to your IT infrastructure has occurred, no data or money was stolen and hopefully your angry customer will believe it was just a “site malfunction”. But as attack methods have become more sophisticated AND more accessible (for example, now one can simply rent hundreds of BOT computer as a service, to carry the attack for him, using a simple interface, with no need to know how to actually hack), the industry had to act, and developed means to mitigate these attacks. Several methods of DDoS mitigation exist and multiple companies offer these as a service. Now a very dangerous equation begins to unfold, one where the attacker can use simple, cheap tools (a fairly typical rate for DDoS botnet rental hovers around the $200 for 10,000 bot agents per day), and the defender must invest much larger resources, both internal (maintaining a Security Operations Center or SOC) and external (service providers), creating an inherent asymmetry. This asymmetry means that organizations wishing to mitigate this threat will keep investing (or throwing, since there is no actual gain here, only minimizing the impact) money over time, until they are in serious economic pain. And this is exactly what Islamic terrorist have been trying to do in the recent global jihad campaign- making western countries bleed money in order to try and prevent sparse attacks carried by rudimentary means. As Osama bin Laden said: “It is very important to concentrate on hitting the American economy with every available tool … the economy is the base of its military power. The United States is a great economy but at the same time it is fragile.” The risk is that using offensive cyber means one can achieve this goal much faster (and one does not have to blow himself to pieces in the process, or hurt innocent people). Therefore, prevention and not only mitigation is necessary. Organizations must be far more proactive than they are now. Sure, investments in IT security and best practices are always a good idea, but also applying preventive intelligence to greatly reduce the impact of attacks. This, couples with harsher legislation and enforcement against both the suppliers and the perpetrators of the attacks will hopefully, in the end, balance this asymmetric equation. For protection against your eCommerce site click here . Source: http://defense-update.com/20131107_denial-service-ddos-cyber-attacks-using-logic-terror-threats.html
Much has been discussed about the damage that the Advanced Persistent Threat (APT) attacks cause to corporates and governments alike. It is estimate that at least 50% of Fortune 500 companies have been compromised by APT, and the potential financial damage to these organizations is almost impossible to quantify, but probably in the trillions of US dollars. Compared to this a crude Denial of Service (DoS) attack or its more advance siblings, the Distributed Denial of Service (DDoS) attacks and Distributed Reflector (DRDoS) attacks, their outcome seems pretty benign- your site is being bombarded by thousands of request for information, until the server gives up and no-one can actually use the site. Once the attack stops, access is possible again and no damage to your IT infrastructure has occurred, no data or money was stolen and hopefully your angry customer will believe it was just a “site malfunction”. But as attack methods have become more sophisticated AND more accessible (for example, now one can simply rent hundreds of BOT computer as a service, to carry the attack for him, using a simple interface, with no need to know how to actually hack), the industry had to act, and developed means to mitigate these attacks. Several methods of DDoS mitigation exist and multiple companies offer these as a service. Now a very dangerous equation begins to unfold, one where the attacker can use simple, cheap tools (a fairly typical rate for DDoS botnet rental hovers around the $200 for 10,000 bot agents per day), and the defender must invest much larger resources, both internal (maintaining a Security Operations Center or SOC) and external (service providers), creating an inherent asymmetry. This asymmetry means that organizations wishing to mitigate this threat will keep investing (or throwing, since there is no actual gain here, only minimizing the impact) money over time, until they are in serious economic pain. And this is exactly what Islamic terrorist have been trying to do in the recent global jihad campaign- making western countries bleed money in order to try and prevent sparse attacks carried by rudimentary means. As Osama bin Laden said: “It is very important to concentrate on hitting the American economy with every available tool … the economy is the base of its military power. The United States is a great economy but at the same time it is fragile.” The risk is that using offensive cyber means one can achieve this goal much faster (and one does not have to blow himself to pieces in the process, or hurt innocent people). Therefore, prevention and not only mitigation is necessary. Organizations must be far more proactive than they are now. Sure, investments in IT security and best practices are always a good idea, but also applying preventive intelligence to greatly reduce the impact of attacks. This, couples with harsher legislation and enforcement against both the suppliers and the perpetrators of the attacks will hopefully, in the end, balance this asymmetric equation. For protection against your eCommerce site click here . Source: http://defense-update.com/20131107_denial-service-ddos-cyber-attacks-using-logic-terror-threats.html 
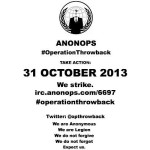 Anonymous hackers, more precisely the ones who hacked a couple of Syrian government websites last week, have announced the start of a new campaign called Operation Throwback. ~ SoftPedia The goal of the operation is “to strike back against the oppressors of our freedom.” The hackers say they will launch distributed denial-of-service (DDOS) attacks against several high-profile websites. Today, on October 28, they plan on launching a cyberattack against the main website of T-Mobile. On October 31, they plan on attacking the website of the FBI, the NSA, Verizon, Microsoft and AT&T. The hacktivists urge their supporters to download DDOS tools and VPNs. The initiators of the operation are providing download links and instructions on how to use them. Earlier today, the hackers tested their “firepower” against the official website of the American Nazi Party. At the time of publishing NCB Interpol web site was down, apparantly from Ddos attack. Source: http://revolution-news.com/opthrowback-anonymous-to-launch-ddos-attacks-against-fbi-nsa/
Anonymous hackers, more precisely the ones who hacked a couple of Syrian government websites last week, have announced the start of a new campaign called Operation Throwback. ~ SoftPedia The goal of the operation is “to strike back against the oppressors of our freedom.” The hackers say they will launch distributed denial-of-service (DDOS) attacks against several high-profile websites. Today, on October 28, they plan on launching a cyberattack against the main website of T-Mobile. On October 31, they plan on attacking the website of the FBI, the NSA, Verizon, Microsoft and AT&T. The hacktivists urge their supporters to download DDOS tools and VPNs. The initiators of the operation are providing download links and instructions on how to use them. Earlier today, the hackers tested their “firepower” against the official website of the American Nazi Party. At the time of publishing NCB Interpol web site was down, apparantly from Ddos attack. Source: http://revolution-news.com/opthrowback-anonymous-to-launch-ddos-attacks-against-fbi-nsa/ 
 The website for the United States National Security Agency suddenly went offline Friday. NSA.gov has been unavailable globally as of late Friday afternoon, and Twitter accounts belonging to people loosely affiliated with the Anonymous hacktivism movement have suggested they are responsible. Twitter users @AnonymousOwn3r and @TruthIzSexy both were quick to comment on the matter, and implied that a distributed denial-of-service attack, or DDoS, may have been waged as an act of protest against the NSA Allegations that those users participated in the DDoS — a method of over-loading a website with too much traffic — are currently unverified, and @AnonymousOwn3r has previously taken credit for downing websites in a similar fashion, although those claims have been largely contested. The crippling of NSA.gov comes amid a series of damning national security documents that have been disclosed without authorization by former intelligence contractor Edward Snowden. The revelations in the leaked documents have impassioned people around the globe outraged by evidence of widespread surveillance operated by the NSA, and a massive “Stop Watching Us” rally is scheduled for Saturday in Washington, DC. DDoS attacks are illegal in the United States under the Computer Fraud and Abuse Act, or CFAA, and two cases are currently underway in California and Virginia in which federal judges are weighing in on instances in which members of Anonymous allegedly used the technique to take down an array of sites during anti-copyright campaigns waged by the group in 2010 and 2011. In those cases, so-called hacktivsits are reported to have conspired together to send immense loads of traffic to targeted websites, rendering them inaccessible due to the overload.
The website for the United States National Security Agency suddenly went offline Friday. NSA.gov has been unavailable globally as of late Friday afternoon, and Twitter accounts belonging to people loosely affiliated with the Anonymous hacktivism movement have suggested they are responsible. Twitter users @AnonymousOwn3r and @TruthIzSexy both were quick to comment on the matter, and implied that a distributed denial-of-service attack, or DDoS, may have been waged as an act of protest against the NSA Allegations that those users participated in the DDoS — a method of over-loading a website with too much traffic — are currently unverified, and @AnonymousOwn3r has previously taken credit for downing websites in a similar fashion, although those claims have been largely contested. The crippling of NSA.gov comes amid a series of damning national security documents that have been disclosed without authorization by former intelligence contractor Edward Snowden. The revelations in the leaked documents have impassioned people around the globe outraged by evidence of widespread surveillance operated by the NSA, and a massive “Stop Watching Us” rally is scheduled for Saturday in Washington, DC. DDoS attacks are illegal in the United States under the Computer Fraud and Abuse Act, or CFAA, and two cases are currently underway in California and Virginia in which federal judges are weighing in on instances in which members of Anonymous allegedly used the technique to take down an array of sites during anti-copyright campaigns waged by the group in 2010 and 2011. In those cases, so-called hacktivsits are reported to have conspired together to send immense loads of traffic to targeted websites, rendering them inaccessible due to the overload.