Follows Collective’s ‘Total War’ Against Donald Trump After earlier this year declaring “total war” against U.S. Republican presidential candidate Donald Trump, the hacktivist group Anonymous is now threatening global banks with 30 days of distributed denial-of-service attack disruptions. As a preview, on May 2, the group claimed to have disrupted the website of Greece’s central bank. “Olympus will fall. A few days ago we declared the revival of Operation Icarus. Today we have continuously taken down the website of the Bank of Greece,” the group said in the video posted on You Tube and delivered in the classic Anonymous style via a disembodied, computerized voice. “This marks the start of a 30-day campaign against central bank sites across the world,” it adds. “Global banking cartel, you’ve probably expected us.” Of course, banks have previously been targeted en masse by DDoS attackers. Beginning in 2012, for example, attacks waged by a group calling itself the “Izz ad-Din al-Qassam Cyber Fighters” continued to disrupt U.S. banks’ websites as part of what it called “Operation Ababil.” In March, the Justice Department unsealed indictments against seven Iranians – allegedly working on behalf of the Iranian government – accusing them of having waged those attacks. Regardless of who was involved, it’s unclear if Anonymous could bring similar DDoS capabilities to bear for its Operation Icarus. A Central Bank of Greece official, who declined to be named, confirmed the May 2 DDoS disruption to Reuters , though said the effect was minimal. “The attack lasted for a few minutes and was successfully tackled by the bank’s security systems. The only thing that was affected by the denial-of-service attack was our website,” the official said. Greek banks have been previously targeted by DDoS extortionists, demanding bitcoins. “It would have been better if no disruption occurred, but it is good that the attack – if that is what caused the disruption – was handled so quickly,” says information security expert Brian Honan, who’s a cybersecurity expert to the EU’s law enforcement intelligence agency, Europol. A “World Banking Cartel Master Target List” published by Anonymous to text-sharing site Pastebin early this month lists the U.S. Federal Reserve, as well as Fed banks in Atlanta, Boston, Chicago, Dallas, Minneapolis, New York, Philadelphia, Richmond and St. Louis. Also on the target list are websites for the International Monetary Fund, the World Bank as well as 158 central banks’ websites. In a related video missive issued March 31, Anonymous urged its members to “take your weapons and aim them at the New York Stock Exchange and Bank of England,” promising that “this is the operation to end all others.” The planned Anonymous operation follows elements of the collective earlier this year declaring “total war” against Trump, and on April 1 temporarily disrupting several of Trump’s websites, The Hill reports. Since then, of course, Trump has become the only Republican presidential candidate left standing after his massive win in this week’s Indiana primary. Banks: Beware DDoS Threats While the Anonymous bark doesn’t always equal its bite, in the wake of this alert, “banks in the United Kingdom, United States and Latin America should be very prepared” against potential attacks, says Carl Herberger, vice president of security for DDoS-mitigation and security firm Radware. “In the same vein as someone yelling ‘bomb’ at an airport or fire at a movie theater, cyber-attack threats – whether idle or not – are not to be taken lightly,” he says, although he adds that the number of threatened DDoS attacks outweighs the quantity of actual attacks. Herberger says in light of the new threat, all banks should review their DDoS defense plans, keeping in mind that DDoS attackers do continue to refine their tactics, as seen in the disruption of Geneva-based encrypted email service ProtonMail. “As the attacks on ProtonMail in November 2015 have demonstrated … attackers change the profile of their attacks frequently and leverage a persistent and advanced tactic of revolving attacks geared to dumbfound detection algorithms,” he says, dubbing such tactics “advanced persistent DoS.” Maintain a DDoS Defense Plan Security experts have long recommended that all organizations have a DDoS defense plan in place. The U.K.’s national fraud and cybercrime reporting center, ActionFraud, for example, recently issued the following advice to all organizations: Review: “Put appropriate threat reduction/mitigation measures in place,” tailored to the risk DDoS disruptions would pose to the organization. Hire: If DDoS attacks are a threat, seek professional help. “If you consider that protection is necessary, speak to a DDoS prevention specialist.” Prepare: All organizations should liaise with their ISP in advance of any attack. “Whether you are at risk of a DDoS attack or not, you should have the hosting facilities in place to handle large, unexpected volumes of website hits.” DDoS Extortions Spike The guidance from ActionFraud, released April 29, also warned that the center has recently seen a spike in DDoS extortion threats from an unnamed “online hacking group” demanding the equivalent of $2,250 to call off their planned attack. “The group has sent emails demanding payment of 5 bitcoins to be paid by a certain time and date. The email states that this demand will increase by 5 bitcoins for each day that it goes unpaid,” ActionFraud’s alert states. “If their demand is not met, they have threatened to launch a [DDoS] attack against the businesses’ websites and networks, taking them offline until payment is made.” ActionFraud advises targeted organizations: “Do not pay the demand.” That echoes longstanding advice from law enforcement agencies globally. ActionFraud also urges organizations to keep all copies of DDoS extortion emails – including complete email headers – as well as a complete timeline for the threats and any attacks, and to immediately report threats or attacks to authorities. Investigators say that keeping complete records – including packet-capture logs – is essential for helping to identify perpetrators. Or as ActionFraud advises: “Keep a timeline of events and save server logs, web logs, email logs, any packet capture, network graphs, reports, etc.” Masquerading as Armada Collective? CloudFlare, a DDoS mitigation firm, reports that related attacks began in March and have been carried out under the banner of Armada Collective, as well as potentially Lizard Squad, although it’s not clear if those groups are actually involved. It’s also unclear if the threatened DDoS disruptions have ever materialized. “We’ve been unable to find a single incident where the current incarnation of the Armada Collective has actually launched a DDoS attack,” CloudFlare CEO Matthew Prince says in a blog post. “In fact, because the extortion emails reuse bitcoin addresses, there’s no way the Armada Collective can tell who has paid and who has not. In spite of that, the cybercrooks have collected hundreds of thousands of dollars in extortion payments.” Source: http://www.bankinfosecurity.com/anonymous-threatens-bank-ddos-disruptions-a-9085
See the article here:
Anonymous Threatens Bank DDoS Disruptions

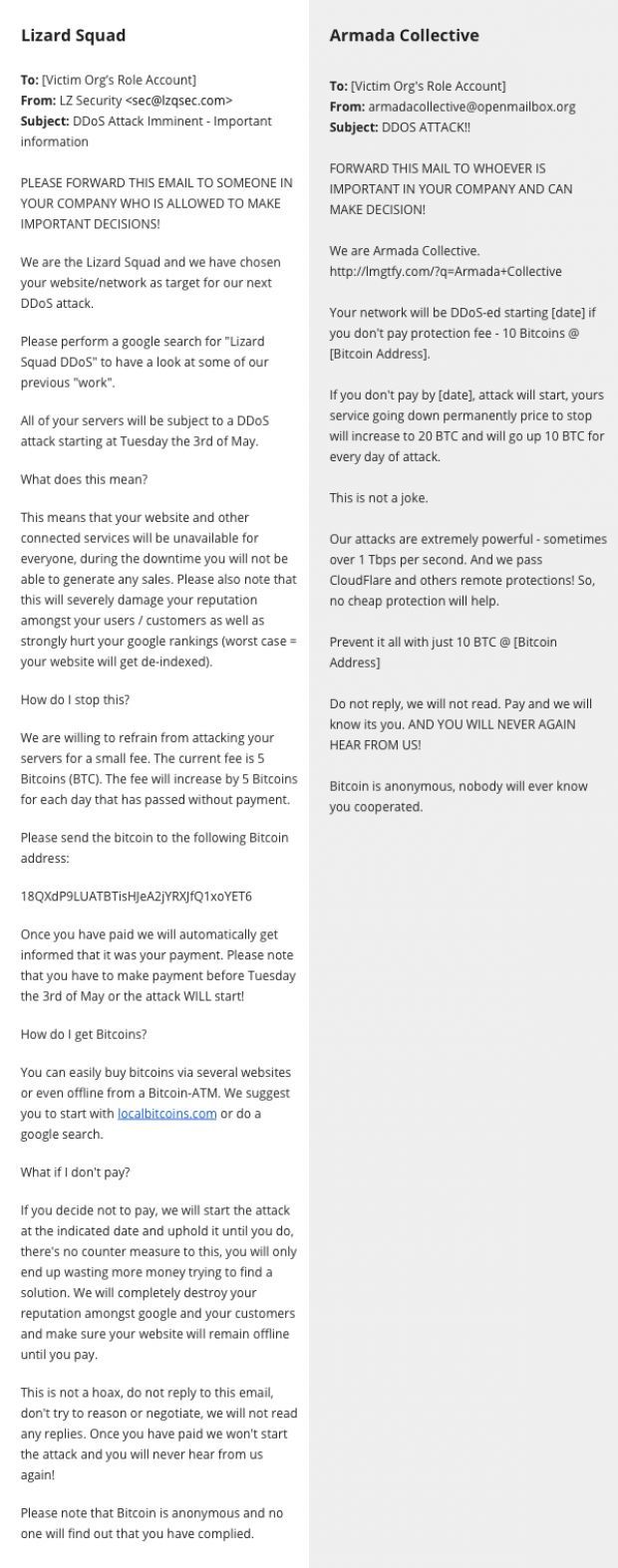
 After terrorizing companies under the fake Armada Collective moniker, the same group appears to have switched to using the name of the infamous Lizard Squad hacking crew, CloudFlare reported today. Early this week on Monday, CloudFlare let everyone know there was a criminal goup sending out extortion emails to companies around the globe. The criminals were posing as Armada Collective , an infamous group known for carrying out DDoS attacks if victims didn’t pay a so-called “protection tax.” The crooks were basing their attacks on the victims googling their name and finding out about the tactics of the real Armada Collective. In fact, CloudFlare says it never saw a single DDoS attack carried out by this group against its targets. In another blog post today, CloudFlare says that three days after they exposed the group, the criminals dropped the Armada Collective name and started using Lizard Squad instead, another hacking crew, famous for downing the Xbox and PlayStation networks on Christmas 2014. The change was to be expected since extorted organizations that would google the Armada Collective name would see all the stories about the copycats instead. CloudFlare says that over 500 companies received extortion emails from this group claiming to be Lizard Squad and that all these emails were identical. As before, the group used one single Bitcoin address to receive payments. By using one Bitcoin address, the group would not be able to tell which companies paid the ransom and which didn’t, meaning this was almost sure the same group as before, launching empty threats once again. CloudFlare says that just like when claiming to be Armada Collective, the group never launched any DDoS attacks when posing as Lizard Squad. Below is a comparison of the two ransom notes received by companies, from the fake Lizard Squad group on the left, and from the fake Armada Collective group on the right. Source: http://justfreedownload.net/news/98693/armada-collective-copycats-now-posing-as-lizard-squad-in-ddos-extortion-scheme.html
After terrorizing companies under the fake Armada Collective moniker, the same group appears to have switched to using the name of the infamous Lizard Squad hacking crew, CloudFlare reported today. Early this week on Monday, CloudFlare let everyone know there was a criminal goup sending out extortion emails to companies around the globe. The criminals were posing as Armada Collective , an infamous group known for carrying out DDoS attacks if victims didn’t pay a so-called “protection tax.” The crooks were basing their attacks on the victims googling their name and finding out about the tactics of the real Armada Collective. In fact, CloudFlare says it never saw a single DDoS attack carried out by this group against its targets. In another blog post today, CloudFlare says that three days after they exposed the group, the criminals dropped the Armada Collective name and started using Lizard Squad instead, another hacking crew, famous for downing the Xbox and PlayStation networks on Christmas 2014. The change was to be expected since extorted organizations that would google the Armada Collective name would see all the stories about the copycats instead. CloudFlare says that over 500 companies received extortion emails from this group claiming to be Lizard Squad and that all these emails were identical. As before, the group used one single Bitcoin address to receive payments. By using one Bitcoin address, the group would not be able to tell which companies paid the ransom and which didn’t, meaning this was almost sure the same group as before, launching empty threats once again. CloudFlare says that just like when claiming to be Armada Collective, the group never launched any DDoS attacks when posing as Lizard Squad. Below is a comparison of the two ransom notes received by companies, from the fake Lizard Squad group on the left, and from the fake Armada Collective group on the right. Source: http://justfreedownload.net/news/98693/armada-collective-copycats-now-posing-as-lizard-squad-in-ddos-extortion-scheme.html 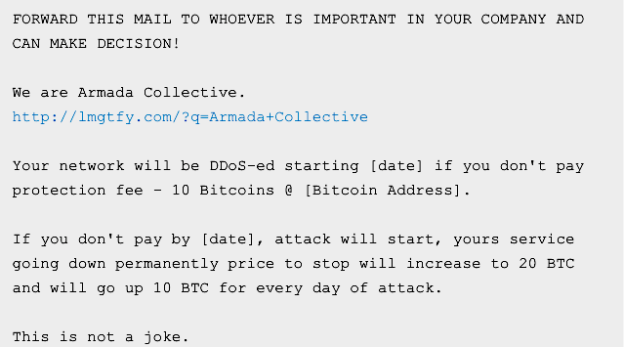
 In less than two months, online businesses have paid more than $100,000 to scammers who set up a fake distributed denial-of-service gang that has yet to launch a single attack. The charlatans sent businesses around the globe extortion e-mails threatening debilitating DDoS attacks unless the recipients paid as much as $23,000 by Bitcoin in protection money, according to a blog post published Monday by CloudFlare, a service that helps protect businesses from such attacks. Stealing the name of an established gang that was well known for waging such extortion rackets, the scammers called themselves the Armada Collective. “If you don’t pay by [date], attack will start, yours service going down permanently price to stop will increase to increase to 20 BTC and will go up 10 BTC for every day of the attack,” the typical demand stated. “This is not a joke.” Except that it was. CloudFlare compared notes with other DDoS mitigation services and none of them could find a single instance of the group acting on its threat. CloudFlare also pointed out that the group asked multiple victims to send precisely the same payment amounts to the same Bitcoin addresses, a lapse that would make it impossible to know which recipients paid the blood money and which ones didn’t. Despite the easily spotted ruse, many businesses appear to have fallen for the scam. According to a security analyst contacted by CloudFlare, Armada Collective Bitcoin addresses have received more than $100,000. “The extortion emails encourage targeted victims to Google for the Armada Collective,” CloudFlare CEO Matthew Prince wrote. “I’m hopeful this article will start appearing near the top of search results and help organizations act more rationally when they receive such a threat.” Source: http://arstechnica.com/security/2016/04/businesses-pay-100000-to-ddos-extortionists-who-never-ddos-anyone/
In less than two months, online businesses have paid more than $100,000 to scammers who set up a fake distributed denial-of-service gang that has yet to launch a single attack. The charlatans sent businesses around the globe extortion e-mails threatening debilitating DDoS attacks unless the recipients paid as much as $23,000 by Bitcoin in protection money, according to a blog post published Monday by CloudFlare, a service that helps protect businesses from such attacks. Stealing the name of an established gang that was well known for waging such extortion rackets, the scammers called themselves the Armada Collective. “If you don’t pay by [date], attack will start, yours service going down permanently price to stop will increase to increase to 20 BTC and will go up 10 BTC for every day of the attack,” the typical demand stated. “This is not a joke.” Except that it was. CloudFlare compared notes with other DDoS mitigation services and none of them could find a single instance of the group acting on its threat. CloudFlare also pointed out that the group asked multiple victims to send precisely the same payment amounts to the same Bitcoin addresses, a lapse that would make it impossible to know which recipients paid the blood money and which ones didn’t. Despite the easily spotted ruse, many businesses appear to have fallen for the scam. According to a security analyst contacted by CloudFlare, Armada Collective Bitcoin addresses have received more than $100,000. “The extortion emails encourage targeted victims to Google for the Armada Collective,” CloudFlare CEO Matthew Prince wrote. “I’m hopeful this article will start appearing near the top of search results and help organizations act more rationally when they receive such a threat.” Source: http://arstechnica.com/security/2016/04/businesses-pay-100000-to-ddos-extortionists-who-never-ddos-anyone/