Critics of the Aquino administration responsible for hacking government websites will be dealt with accordingly, Malacañang warned yesterday. “There are existing laws against hacking and proper action will be taken,” Press Secretary Herminio Coloma told a news briefing when sought for comment on the latest attacks on the websites of several government agencies by activist hacker group Anonymous Philippines. “There are sufficient avenues for free expression so there is no need to resort to illegal acts such as hacking of government websites,” Coloma said. He said that sentiments against the government could be aired in street protests. According to Coloma, there is enough “democratic space” where the public can air their grievances. More gov’t sites under attack Anonymous Philippines claimed it has stopped the operation of major government websites as hackers geared up for today’s “Million Mask March” in Quezon City. In a post on its Facebook page yesterday, the group said the websites of around 100 local and national government agencies – including that of the Official Gazette, Senate, House of Representatives and the National Bureau of Investigation – were “currently down.” With the exception of the Senate website (senate.gov.ph), a random check showed that most of the national government websites in the list were accessible as of yesterday afternoon. Despite having a security feature to mitigate attacks, the Official Gazette website (gov.ph) was temporarily inaccessible yesterday. In a phone interview with The STAR, Roy Espiritu of the Information and Communications Technology Office confirmed that a number of government sites have been under distributed denial of service (DDoS) attacks since Monday. However, he said that “critical” government websites are “secure.” Espiritu said government websites are currently in the process of migrating into more secure servers as mandated by Administrative Order 39, signed by the President in July, which establishes a Government Web Hosting Service. The service seeks to “ensure the government’s Internet presence around the clock under all foreseeable conditions.” Earlier, Espiritu said they are looking into the possibility of incorporating security measures to beef up the defenses of government websites. A DDoS attack is mounted to shut down an Internet site by flooding it with access requests and overload its server handling capabilities. Websites affected by successful DDoS attacks are inaccessible to legitimate users who wish to view their content. The Official Gazette website is protected from DDoS attacks by CloudFare, which offers security by checking the integrity of browsers and looking for threat signatures from users who wish to access the site. DDoS attacks are dependent on the number of people trying to access the website at the same time. Espiritu earlier said that even the most secure websites could be affected by such attacks. In 2010, the websites of Visa and MasterCard were affected by a DDoS attack mounted by supporters of whistle-blower organization WikiLeaks. DDoS attacks are different from hacking, which requires an Internet user to access the website using the password of a legitimate administrator. Investigation According to Espiritu, an investigation will be conducted to determine the people behind the attacks on government websites. He said the people behind the attacks may be charged under the e-Commerce law as the move to shut down the websites deprived the public of the information that they need from the government. On Monday, the website of the Office of the Ombudsman was defaced by people claiming to be members of Anonymous Philippines. The latest cyber attacks on government websites came amid issues involving alleged misuse of the Priority Development Assistance Fund and the Disbursement Acceleration Program of the legislative and the executive, respectively. In August, various government sites were hacked during the Million People March attended by thousands in Luneta. Previous incidents of attacks happened during the height of discussions on various issues such as the passage of the Cybercrime Prevention Law and the territorial dispute with China. Worldwide protest The Million Mask March is an event that will be held in various locations around the globe today “to remind this world what it has forgotten. That fairness, justice, and freedom are more than just words.” According to its official Facebook page, the march will cover various topics including government, education reform, constitutional rights, freedom, unity, drug abuse, respect for all, corruption, nutrition and health and violence among children, among others. Based on the events page of the Million Mask March-Philippines, over 1,000 Facebook users have confirmed attendance in today’s march. A post by an Anonymous member said participants will meet at the Quezon Memorial Circle at 8 a.m. to discuss the activities for the day. The march will start in front of the Sandiganbayan along Commonwealth Avenue to Batasang Pambansa. In a text message to The STAR, Quezon City department of public order and safety chief Elmo San Diego said they received no application for a permit to hold a rally or a march near Batasang Pambansa today. The Anonymous member reminded participants not to bring any form of weapon, adding that the event will be held to show the public’s reaction to the mishandling of the government committed by people in power. The Department of Science and Technology (DOST) Information and Communications Technology Office yesterday underscored the need to fast track efforts to set up a more secure government website hosting facility following the latest hacking of government websites. The websites of the Insurance Commission, Southern Philippines Development Authority, Optical Media Board and that of the local government units of Bolinao, Pasig City, Pateros and the municipality of Basnud, Oriental Mindoro were defaced by members of Anonymous Philippines. Source: http://www.philstar.com/headlines/2013/11/05/1253167/palace-act-vs-hackers
Read More:
Anonymous Philippines hack and DDoS Government sites


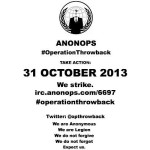 Anonymous hackers, more precisely the ones who hacked a couple of Syrian government websites last week, have announced the start of a new campaign called Operation Throwback. ~ SoftPedia The goal of the operation is “to strike back against the oppressors of our freedom.” The hackers say they will launch distributed denial-of-service (DDOS) attacks against several high-profile websites. Today, on October 28, they plan on launching a cyberattack against the main website of T-Mobile. On October 31, they plan on attacking the website of the FBI, the NSA, Verizon, Microsoft and AT&T. The hacktivists urge their supporters to download DDOS tools and VPNs. The initiators of the operation are providing download links and instructions on how to use them. Earlier today, the hackers tested their “firepower” against the official website of the American Nazi Party. At the time of publishing NCB Interpol web site was down, apparantly from Ddos attack. Source: http://revolution-news.com/opthrowback-anonymous-to-launch-ddos-attacks-against-fbi-nsa/
Anonymous hackers, more precisely the ones who hacked a couple of Syrian government websites last week, have announced the start of a new campaign called Operation Throwback. ~ SoftPedia The goal of the operation is “to strike back against the oppressors of our freedom.” The hackers say they will launch distributed denial-of-service (DDOS) attacks against several high-profile websites. Today, on October 28, they plan on launching a cyberattack against the main website of T-Mobile. On October 31, they plan on attacking the website of the FBI, the NSA, Verizon, Microsoft and AT&T. The hacktivists urge their supporters to download DDOS tools and VPNs. The initiators of the operation are providing download links and instructions on how to use them. Earlier today, the hackers tested their “firepower” against the official website of the American Nazi Party. At the time of publishing NCB Interpol web site was down, apparantly from Ddos attack. Source: http://revolution-news.com/opthrowback-anonymous-to-launch-ddos-attacks-against-fbi-nsa/ 
 The website for the United States National Security Agency suddenly went offline Friday. NSA.gov has been unavailable globally as of late Friday afternoon, and Twitter accounts belonging to people loosely affiliated with the Anonymous hacktivism movement have suggested they are responsible. Twitter users @AnonymousOwn3r and @TruthIzSexy both were quick to comment on the matter, and implied that a distributed denial-of-service attack, or DDoS, may have been waged as an act of protest against the NSA Allegations that those users participated in the DDoS — a method of over-loading a website with too much traffic — are currently unverified, and @AnonymousOwn3r has previously taken credit for downing websites in a similar fashion, although those claims have been largely contested. The crippling of NSA.gov comes amid a series of damning national security documents that have been disclosed without authorization by former intelligence contractor Edward Snowden. The revelations in the leaked documents have impassioned people around the globe outraged by evidence of widespread surveillance operated by the NSA, and a massive “Stop Watching Us” rally is scheduled for Saturday in Washington, DC. DDoS attacks are illegal in the United States under the Computer Fraud and Abuse Act, or CFAA, and two cases are currently underway in California and Virginia in which federal judges are weighing in on instances in which members of Anonymous allegedly used the technique to take down an array of sites during anti-copyright campaigns waged by the group in 2010 and 2011. In those cases, so-called hacktivsits are reported to have conspired together to send immense loads of traffic to targeted websites, rendering them inaccessible due to the overload.
The website for the United States National Security Agency suddenly went offline Friday. NSA.gov has been unavailable globally as of late Friday afternoon, and Twitter accounts belonging to people loosely affiliated with the Anonymous hacktivism movement have suggested they are responsible. Twitter users @AnonymousOwn3r and @TruthIzSexy both were quick to comment on the matter, and implied that a distributed denial-of-service attack, or DDoS, may have been waged as an act of protest against the NSA Allegations that those users participated in the DDoS — a method of over-loading a website with too much traffic — are currently unverified, and @AnonymousOwn3r has previously taken credit for downing websites in a similar fashion, although those claims have been largely contested. The crippling of NSA.gov comes amid a series of damning national security documents that have been disclosed without authorization by former intelligence contractor Edward Snowden. The revelations in the leaked documents have impassioned people around the globe outraged by evidence of widespread surveillance operated by the NSA, and a massive “Stop Watching Us” rally is scheduled for Saturday in Washington, DC. DDoS attacks are illegal in the United States under the Computer Fraud and Abuse Act, or CFAA, and two cases are currently underway in California and Virginia in which federal judges are weighing in on instances in which members of Anonymous allegedly used the technique to take down an array of sites during anti-copyright campaigns waged by the group in 2010 and 2011. In those cases, so-called hacktivsits are reported to have conspired together to send immense loads of traffic to targeted websites, rendering them inaccessible due to the overload.