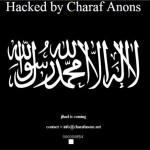
 Islamist element in attacks. A pro-Islamic, anti-American hacking campaign appears to have jumped the gun and started early with hundreds of sites being compromised today. Set to take place on May 7 this month – thought to be US time – and targeting government sites in the US, Israel and India, the campaign is called #OpUSA. It is coordinated mainly through Twitter and postings on sites like Pastebin, with an unknown amount of participants. However, lists of compromised sites are already apppearing, with a group called “X-Blackerz Inc” claiming to have hacked “100 US websites”, posting anti-American messages. iTnews loaded some of the sites listed which have India-related domain names, and found them defaced. Elswhere, a group calling itself Charaf Anons posted a list of 73 defaced sites on Pastebin. The website of the Honolulu, Hawaii Police Department was also claimed to be hacked, but as of writing, it is not defaced and operates normally. However, the hackers say they have captured databases that include the Honolulu Police Department staff logins and passwords. Another one was also posted with names and phone numbers that iTnews was able to verify as belonging to police officers in Honolulu. There is more to come: on May 7, the hackers are threatening to release a trove of “all governments emails of USA” [sic] captured by them. From the Anonghost Twitter account Security researcher Analysis Intelligence believes OpUSA features “self-proclaimed online freedom fighters” such as the Pakistani ZCompany Hacking Crew and Palestinians Izz ad-Din al-Qassam Cyber Fighters. These and other groups have hacked thousands of websites in the past, leaked credit card information for American and Israeli individuals and launched denial of service attacks against US banks, according to Analysis Intelligence. The motive for the OpUSA attacks are political, seeking revenge against drone attacks and military action in Iraq, Afghanistan, Gaza and Pakistan, the analysts believe. For DDoS protection click here . Source: http://www.itnews.com.au/News/342192,opusa-hacking-spree-kicks-off-early.aspx
Islamist element in attacks. A pro-Islamic, anti-American hacking campaign appears to have jumped the gun and started early with hundreds of sites being compromised today. Set to take place on May 7 this month – thought to be US time – and targeting government sites in the US, Israel and India, the campaign is called #OpUSA. It is coordinated mainly through Twitter and postings on sites like Pastebin, with an unknown amount of participants. However, lists of compromised sites are already apppearing, with a group called “X-Blackerz Inc” claiming to have hacked “100 US websites”, posting anti-American messages. iTnews loaded some of the sites listed which have India-related domain names, and found them defaced. Elswhere, a group calling itself Charaf Anons posted a list of 73 defaced sites on Pastebin. The website of the Honolulu, Hawaii Police Department was also claimed to be hacked, but as of writing, it is not defaced and operates normally. However, the hackers say they have captured databases that include the Honolulu Police Department staff logins and passwords. Another one was also posted with names and phone numbers that iTnews was able to verify as belonging to police officers in Honolulu. There is more to come: on May 7, the hackers are threatening to release a trove of “all governments emails of USA” [sic] captured by them. From the Anonghost Twitter account Security researcher Analysis Intelligence believes OpUSA features “self-proclaimed online freedom fighters” such as the Pakistani ZCompany Hacking Crew and Palestinians Izz ad-Din al-Qassam Cyber Fighters. These and other groups have hacked thousands of websites in the past, leaked credit card information for American and Israeli individuals and launched denial of service attacks against US banks, according to Analysis Intelligence. The motive for the OpUSA attacks are political, seeking revenge against drone attacks and military action in Iraq, Afghanistan, Gaza and Pakistan, the analysts believe. For DDoS protection click here . Source: http://www.itnews.com.au/News/342192,opusa-hacking-spree-kicks-off-early.aspx
See more here:
May 7 2013 – OpUSA hacking spree kicks off early

