Just as one type of attack against U.S. banks has subsided, the banks are being warned to get ready for another, called “Project Blitzkrieg,” aimed at online theft. Iran denies launching cyberattacks on U.S. banks The distributed-denial-of-service (DDoS) attacks that briefly disrupted the online services of a half-dozen major financial institutions late last month — Wells Fargo, U.S. Bancorp, PNC Financial Services Group, Citigroup, Bank of America and JPMorgan Chase — ended abruptly about two weeks ago, even though the group that claimed credit for them had threatened to continue them. Izz al-Din al-Qassam Cyber Fighters, the military wing of Hamas, the Islamic party that governs the Gaza Strip, had said in a Pastebin message that the attacks would continue until a trailer of the independent film “Innocence of Muslims,” which they said insults the prophet Mohammed, was taken off the Internet. But now, says a blog post by Mor Ahuvia, cybercrime communication specialist at security firm RSA, another wave of attacks is looming, this one aimed at stealing big money. “A cyber gang has recently communicated its plans to launch a Trojan attack spree on 30 American banks as part of a large-scale orchestrated crimeware campaign,” Ahuvia wrote. “Planned for this fall, the blitzkrieg-like series of Trojan attacks is set to be carried out by approximately 100 botmasters. RSA believes this is the making of the most substantial organized banking-Trojan operation seen to date.” RSA said the gang leadership appears to come from Russia, and plans to use a “Gozi-like Trojan” that RSA is calling Gozi Prinimalka. Prinimalka is derived from the Russian word meaning “to receive.” “According to underground chatter, the gang plans to deploy the Trojan in an effort to complete fraudulent wire transfers via Man-In-The-Middle (MiTM) manual session-hijacking scenarios,” Ahuvia wrote. “If successfully launched, the full force of this mega heist may only be felt by targeted banks in a month or two. The spree’s longevity, in turn, will depend on how fast banks and their security teams implement countermeasures against the heretofore-secret banking-Trojan,” she wrote. Brian Krebs, who writes the blog KrebsonSecurity, said in a recent post that the RSA analysis “seemed to merely scratch the surface of a larger enterprise that speaks volumes about why online attacks are becoming bolder and more brash toward Western targets.” But he also said this particular threat could be a hoax — that there is some suspicion in the cybercrime world that it could be a sting operation by Russian law enforcement, since the announcement has been so public. Krebs said the threat appears to be coming from a series of posts on Underweb forums by a Russian hacker nicknamed “vorVzakone.” His name translates to “thief-in-law,” which Krebs said, “in Russia and Eastern Europe refers to an entire subculture of elite criminal gangs that operate beyond the reach of traditional law enforcement. The term is sometimes also used to refer to a single criminal kingpin.” Krebs said vorVzakone called the campaign “Project Blitzkrieg,” and according to a translation of one of his messages, said he hopes to recruit 100 botmasters to take advantage of authentication weaknesses in U.S. bank systems before they can improve their protection. The botmasters would have to qualify with an online interview and be trained, and would then get to share in the profits. In vorVzakone’s message, he said: “The development of the system took 4 years of daily work and around $500.000 was spent. Since 2008 by using this product not less than $5m was transferred just by one team.” Jason Healey of the Atlantic Council, a cybercrime expert and former White House security official, said it sounds to him like the group is “trying to be the Russian online equivalent of Ocean’s Eleven — call it Ocean’s Odinnadsat’ — or a group that wants to be seen in that light. They can get some cool points, either way.” Most security experts say the financial sector is the best prepared of any in the U.S. to deal with direct attacks. But these attacks will, of course, not be aimed directly at the banks, but at their customers. And vorVzakone also wrote that the operation will flood cyberheist victim phone lines while the victims are being robbed, in an effort to prevent account holders from receiving confirmation calls or text messages from their banks.” In an interview, Brian Krebs said cyber thieves, “almost always target the line of least resistance, and that is the customer. That doesn’t excuse the banks from their obligation to be constantly upgrading their defenses against such attacks. There are thousands of financial institutions in the U.S. and many of them are woefully behind in updating their customer-facing security measures.” He noted that banking law does not protect commercial and business customers at the same level as individual customers, and said banks need to do much better at flagging abnormal transaction behavior, such as, “a sudden addition of many new employees to an organization’s payroll, particularly if those people are spread all over the country geographically.” “You’d be amazed at how many times a month some bank lets this happen, and with disastrous results,” Krebs said. Still, if vorVzakone and his presumed colleagues are serious about their plan, why broadcast it so blatantly? Is that an indication that the whole thing may be a fraud? Krebs said there is reason for skepticism, noting in his blog post that vorVzakone even posted a homemade movie on YouTube, in which he. “introduces himself as ‘Sergey,’ the stocky bald guy in the sunglasses. He also introduces a hacker who needs little introduction in the Russian underground — a well-known individual who used the nickname ‘NSD.’” Krebs then quotes one Russian expert saying vorVzakone’s “language and demeanor is that of street corner drug dealer or a night club bouncer,” not someone who can organize and run a sophisticated cyberheist operation. Krebs himself is not quite as harsh, but said such projects “are announced all the time on the underground, but usually they are in fairly closed, secretive forums. The forums on which this project was announced were moderately secret, but it’s fairly unusual for miscreants to create YouTube videos of such projects and to promote them so openly.” Healey said the public bragging is a mistake. “To succeed with a Trojan, you want it to be somewhat secret with few people involved,” he said. “The few who are involved should be well known and trustworthy. That is the opposite of what Ocean’s Odinnadsat’ has done.” He said that and the fact that they are recruiting people who may be unknown to them “makes it more likely that the intel and threat companies, and law enforcement, can get the code beforehand.” Another problem that could undermine the operation is simple organizational weaknesses. “My sense is that such a project would require a decent amount of operational cohesion and security, and cooperation,” Krebs said. “From what I’ve seen of the underground, the more people you involve in a scheme, the more likely it is to fall apart.” But he said whether this threat is real or not, the need for protection is crucial. The best way for customers to avoid theft is to prevent their computer from being infected. “The trouble is,” Krebs said. “It’s becoming increasingly difficult to tell when a system is or is not infected. That’s why I advocate the use of a Live CD approach to online banking. That way, even if the underlying hard drive is infected with a remote-access, password stealing Trojan like Gozi, your online banking session is protected.” Source: http://www.networkworld.com/news/2012/101012-us-banks-warned-of-another-263227.html?page=1
Continue reading here:
U.S. banks warned of another Distributed Denial of Service ‘DDoS’ attack

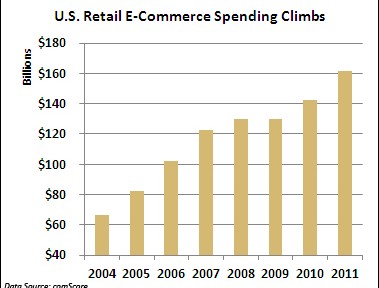
 A string of cyber attacks on U.S. financial institutions has created headaches this fall by slowing down or preventing online banking access for millions of Americans. But imagine the real economic damage that similar-style attacks would cause if they struck U.S. retailers this holiday-shopping season, potentially eating into projected online sales of $54 billion. While retailers deserve credit for bolstering their defenses against credit-card-hungry organized crime rings, security professionals believe the industry is vulnerable to this different kind of onslaught aimed at crippling online sales. “The gloves are off in cyber space. The reality is if they want it to get worse, it can get worse,” said Dave Aitel, a former computer scientist at the National Security Agency. “I don’t think people are really prepared mentally to what happens if Amazon goes down.” Unlike the ongoing cyber attacks against U.S. banks, there doesn’t appear to be a specific cyber threat against retailers. Yet there are concerns that retailers aren’t ready for denial-of-service (DDoS) attacks from a powerful state actor like Iran, which many in the U.S. government suspect had a hand in the recent attacks on financial institutions like Bank of America (BAC) and J.P. Morgan Chase (JPM). “The Iranians are in the business of making a point and the bank attacks are not likely to have the impact they need, hence retailers are the next most likely target, especially in the holiday season,” said Aitel, CEO of Immunity, a cyber security firm that works with Fortune 500 companies. Online Sales Exceed $160B It’s hard to overstate the importance of e-commerce in today’s smartphone and social network dominated world. According to comScore (CSOR), annual U.S. retail e-commerce spending has surged 143% since 2004 to $161.52 billion last year. Despite the sluggish domestic economy and tepid retail sales growth, e-commerce spending jumped 13% between 2010 and 2011. Online shopping is crucial during the all-important holiday-shopping season. E-commerce spending rose 14% last holiday season to $37.2 billion, comScore said. In the face of continued economic uncertainty, online spending is projected to climb 17% this season to $54.47 billion, according to MarketLive. “It’s very important for any retailer to have a web presence or you risk being left out in the cold,” said Andrew Lipsman, vice president of industry analysis at comScore, who noted that even in-person purchases typically originate online. Adapting to Shifting Threat Security professionals believe retailers’ cyber defenses are more porous than those of financial institutions — and even some banks succumbed to relentless DDoS attacks this fall. Given their prior experience combating thieves in Russia and elsewhere trying to siphon funds or snatch credit-card numbers, retailers aren’t really positioned to halt massive DDoS attacks from powerful state actors like Iran. “That’s a very different threat and in many ways is more severe,” said Aitel. “They’re not thinking: What if it’s not about the money? What if someone wants to take me out just to take me out?” Cedric Leighton, a former NSA official, said he agrees that retailers are not as well prepared as their financial peers. “I don’t think they’ve gotten to the point where they can truly say their whole cyber supply chain is as well secured as they need to be in this day and age,” said Leighton, CEO of a Washington, D.C.-based risk-management consultancy. Leighton said hackers could also disrupt companies’ supply chains by messing with order quantities and locations, creating costly problems for retailers. Just this week Barnes & Noble (BKS) fell victim to a very sophisticated criminal attack that may have resulted in stolen credit and debit card information at 63 of its stores. Amazon Atop Target List The importance of a robust cyber defense is even more important for online retailers like Amazon.com and Overstock (OSTK). “If they aren’t available online, there is no business. They don’t exist,” said Ronen Kenig, director of security product marketing at Tel Aviv-based security firm Radware (RDWR). In a potential cyber attack on U.S. retailers, Amazon.com would clearly be the biggest prize. The Seattle company generated $17.4 billion in revenue last holiday quarter. “When you attack the United States you don’t attack Topeka, Kansas,” said Aitel. “Amazon is the big boy on the block. They are of course also the best protected.” Amazon.com and Wal-Mart (WMT) declined to comment for this story, while Target (TGT) didn’t respond to a request for comment. “Every company is going to look at what its exposure is. The greater the company is placed at risk, then the more they are going to invest in trying to protect themselves,” said Mallory Duncan, general counsel at the National Retail Federation. Noting that some companies “rely extremely heavily on the Internet,” Duncan said, “When you have a bet-the-company type of situation, they’re going to take extraordinary steps to protect that channel.” Cyber Monday in Focus Aitel suggested the days around Cyber Monday — the first work day after Black Friday — as a time when retailers need to be particularly vigilant about the cyber threat. According to comScore, U.S. e-commerce spending on Cyber Monday rose 22% last year to $1.25 billion, making it the highest online spending day in history. “The attackers always like to choose the worst time for the victim,” said Kenig. Bolstering Cyber Defenses So what specifically should retailers be doing to prevent or mitigate the impact of DDoS attacks this holiday season? Leighton said it’s crucial for companies to implement redundant systems with backups that allow switching from one system to the other when necessary. From a bigger picture standpoint, retailers should strive to install security programs that go above and beyond industry security standards, which Aitel said “are really the bottom bar.” Security professionals have been particularly alarmed by some recent cyber attacks that inflicted damage on physical assets, including a devastating attack unleashed on Saudi Arabia’s state run oil company Saudi Aramco Some believe Iran may have been behind this attack, which destroyed an estimated 30,000 computers. Aitel said, “Companies have to look at what happened to Saudi Aramco and say: What would we do if that happened to us? Until they have a good answer for that, they shouldn’t be sleeping that well.” For advanced DDoS protection against your eCommerce site click here . Source: http://www.foxbusiness.com/industries/2012/10/24/would-cyber-attacks-ruin-christmas-for-retailers/
A string of cyber attacks on U.S. financial institutions has created headaches this fall by slowing down or preventing online banking access for millions of Americans. But imagine the real economic damage that similar-style attacks would cause if they struck U.S. retailers this holiday-shopping season, potentially eating into projected online sales of $54 billion. While retailers deserve credit for bolstering their defenses against credit-card-hungry organized crime rings, security professionals believe the industry is vulnerable to this different kind of onslaught aimed at crippling online sales. “The gloves are off in cyber space. The reality is if they want it to get worse, it can get worse,” said Dave Aitel, a former computer scientist at the National Security Agency. “I don’t think people are really prepared mentally to what happens if Amazon goes down.” Unlike the ongoing cyber attacks against U.S. banks, there doesn’t appear to be a specific cyber threat against retailers. Yet there are concerns that retailers aren’t ready for denial-of-service (DDoS) attacks from a powerful state actor like Iran, which many in the U.S. government suspect had a hand in the recent attacks on financial institutions like Bank of America (BAC) and J.P. Morgan Chase (JPM). “The Iranians are in the business of making a point and the bank attacks are not likely to have the impact they need, hence retailers are the next most likely target, especially in the holiday season,” said Aitel, CEO of Immunity, a cyber security firm that works with Fortune 500 companies. Online Sales Exceed $160B It’s hard to overstate the importance of e-commerce in today’s smartphone and social network dominated world. According to comScore (CSOR), annual U.S. retail e-commerce spending has surged 143% since 2004 to $161.52 billion last year. Despite the sluggish domestic economy and tepid retail sales growth, e-commerce spending jumped 13% between 2010 and 2011. Online shopping is crucial during the all-important holiday-shopping season. E-commerce spending rose 14% last holiday season to $37.2 billion, comScore said. In the face of continued economic uncertainty, online spending is projected to climb 17% this season to $54.47 billion, according to MarketLive. “It’s very important for any retailer to have a web presence or you risk being left out in the cold,” said Andrew Lipsman, vice president of industry analysis at comScore, who noted that even in-person purchases typically originate online. Adapting to Shifting Threat Security professionals believe retailers’ cyber defenses are more porous than those of financial institutions — and even some banks succumbed to relentless DDoS attacks this fall. Given their prior experience combating thieves in Russia and elsewhere trying to siphon funds or snatch credit-card numbers, retailers aren’t really positioned to halt massive DDoS attacks from powerful state actors like Iran. “That’s a very different threat and in many ways is more severe,” said Aitel. “They’re not thinking: What if it’s not about the money? What if someone wants to take me out just to take me out?” Cedric Leighton, a former NSA official, said he agrees that retailers are not as well prepared as their financial peers. “I don’t think they’ve gotten to the point where they can truly say their whole cyber supply chain is as well secured as they need to be in this day and age,” said Leighton, CEO of a Washington, D.C.-based risk-management consultancy. Leighton said hackers could also disrupt companies’ supply chains by messing with order quantities and locations, creating costly problems for retailers. Just this week Barnes & Noble (BKS) fell victim to a very sophisticated criminal attack that may have resulted in stolen credit and debit card information at 63 of its stores. Amazon Atop Target List The importance of a robust cyber defense is even more important for online retailers like Amazon.com and Overstock (OSTK). “If they aren’t available online, there is no business. They don’t exist,” said Ronen Kenig, director of security product marketing at Tel Aviv-based security firm Radware (RDWR). In a potential cyber attack on U.S. retailers, Amazon.com would clearly be the biggest prize. The Seattle company generated $17.4 billion in revenue last holiday quarter. “When you attack the United States you don’t attack Topeka, Kansas,” said Aitel. “Amazon is the big boy on the block. They are of course also the best protected.” Amazon.com and Wal-Mart (WMT) declined to comment for this story, while Target (TGT) didn’t respond to a request for comment. “Every company is going to look at what its exposure is. The greater the company is placed at risk, then the more they are going to invest in trying to protect themselves,” said Mallory Duncan, general counsel at the National Retail Federation. Noting that some companies “rely extremely heavily on the Internet,” Duncan said, “When you have a bet-the-company type of situation, they’re going to take extraordinary steps to protect that channel.” Cyber Monday in Focus Aitel suggested the days around Cyber Monday — the first work day after Black Friday — as a time when retailers need to be particularly vigilant about the cyber threat. According to comScore, U.S. e-commerce spending on Cyber Monday rose 22% last year to $1.25 billion, making it the highest online spending day in history. “The attackers always like to choose the worst time for the victim,” said Kenig. Bolstering Cyber Defenses So what specifically should retailers be doing to prevent or mitigate the impact of DDoS attacks this holiday season? Leighton said it’s crucial for companies to implement redundant systems with backups that allow switching from one system to the other when necessary. From a bigger picture standpoint, retailers should strive to install security programs that go above and beyond industry security standards, which Aitel said “are really the bottom bar.” Security professionals have been particularly alarmed by some recent cyber attacks that inflicted damage on physical assets, including a devastating attack unleashed on Saudi Arabia’s state run oil company Saudi Aramco Some believe Iran may have been behind this attack, which destroyed an estimated 30,000 computers. Aitel said, “Companies have to look at what happened to Saudi Aramco and say: What would we do if that happened to us? Until they have a good answer for that, they shouldn’t be sleeping that well.” For advanced DDoS protection against your eCommerce site click here . Source: http://www.foxbusiness.com/industries/2012/10/24/would-cyber-attacks-ruin-christmas-for-retailers/