An analysis of conversations in one of the largest known hacker forums – with around 250,000 members – has revealed that SQL-injection and DDoS are the subjects of most interest to up-and-coming wannabe hackers. In its analysis of the forum (together with 17 other, smaller forums) to be published today, Imperva notes that this “is not a hardcore crime site, but it’s not entirely softcore. New hackers come to this site to learn and, on the other hand, more experienced hackers teach to gain ‘street cred’ and recognition… Typically, once hackers have gained enough of a reputation, they go to a more hardcore, invitation-only forum.” The real value of the analysis is that it shows what tomorrow’s hackers are learning today. “By examining what information hackers seek out or share in these forums, we can better understand where they are focusing their efforts,” explained Amichai Shulman, Imperva’s CTO. It seems that DDoS and SQL injection attacks are the current focus. Each tied at 19% of all discussed attack methodologies. DDoS is rarely out of the news, with hacktivists using it to make political protests, criminals using it to disguise other attacks, and (potentially) nation states using it to disrupt critical infrastructures. The recent spate of attacks against American banks is thought by many to be a politically-inspired attack by Iranian attackers. SQL injection attacks have a slightly lower profile but are similarly popular with criminals – and the same US banks have recently been warned about Havij, an automated SQL injection attack tool (itself a common subject of discussion in the chat forums). Such attacks can be mitigated (and Imperva has discussed this in an earlier blog this month). Nevertheless, the company believes that only 5% of industry’s current security budget is spent on defeating this type of attack; which may help explain why it is so popular. Other subjects disclosed by the Imperva analysis include the growing black market for social media endorsements, especially likes on Facebook and followers on Twitter. Since the social media sites are becoming better at recognizing and excluding automated bots that accrue such ‘currency’, the underground is providing it as a service, with numerous advertisements for buying or selling “illegitimate social network likes, followers, and endorsements” appearing on the forums. But there are also many discussion threads, says Imperva, that include “requests to hack someone’s Facebook profile, usually to settle personal matters. Common examples are spying on one’s girlfriend/ex, taking revenge, and just for lulz.” E-whoring has also become rampant. “With more than 13,000 threads in the dedicated forum we monitor, e-whoring is surely becoming one of the most common methods for beginner cyber criminals to gain easy money.” It’s basically social engineering where an attacker of either sex pretends to be a ‘hot gal with pics’. Dj Co2 posted an explanation on Black Hat World last month: “So what you will be doing is making a girls profile, add some hot pictures and make it look real. You will then be sending messages to different guys (there’s no limit on that). You will then chat with them, make them a little horny and desperate and then get them to sign up through your affiliate link to some webcam site. Tell them that if they buy tokens they can have a private chat with you on the website… 20 Instagram accounts with profile picture for $10.” “The victim,” says Imperva, “is paying for the illusion of a brief relationship.” Men “would be better off getting to know the girl next door,” it suggests. For more information on SQL injection click here . Source: http://www.infosecurity-magazine.com/view/29033/ddos-and-sql-injection-are-the-most-popular-attack-subjects
Read More:
Distributed Denial of Service ‘DDoS’ attack and SQL injection are the most popular attack subjects

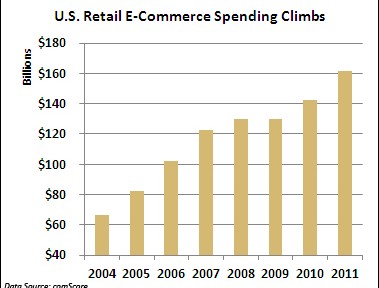
 A string of cyber attacks on U.S. financial institutions has created headaches this fall by slowing down or preventing online banking access for millions of Americans. But imagine the real economic damage that similar-style attacks would cause if they struck U.S. retailers this holiday-shopping season, potentially eating into projected online sales of $54 billion. While retailers deserve credit for bolstering their defenses against credit-card-hungry organized crime rings, security professionals believe the industry is vulnerable to this different kind of onslaught aimed at crippling online sales. “The gloves are off in cyber space. The reality is if they want it to get worse, it can get worse,” said Dave Aitel, a former computer scientist at the National Security Agency. “I don’t think people are really prepared mentally to what happens if Amazon goes down.” Unlike the ongoing cyber attacks against U.S. banks, there doesn’t appear to be a specific cyber threat against retailers. Yet there are concerns that retailers aren’t ready for denial-of-service (DDoS) attacks from a powerful state actor like Iran, which many in the U.S. government suspect had a hand in the recent attacks on financial institutions like Bank of America (BAC) and J.P. Morgan Chase (JPM). “The Iranians are in the business of making a point and the bank attacks are not likely to have the impact they need, hence retailers are the next most likely target, especially in the holiday season,” said Aitel, CEO of Immunity, a cyber security firm that works with Fortune 500 companies. Online Sales Exceed $160B It’s hard to overstate the importance of e-commerce in today’s smartphone and social network dominated world. According to comScore (CSOR), annual U.S. retail e-commerce spending has surged 143% since 2004 to $161.52 billion last year. Despite the sluggish domestic economy and tepid retail sales growth, e-commerce spending jumped 13% between 2010 and 2011. Online shopping is crucial during the all-important holiday-shopping season. E-commerce spending rose 14% last holiday season to $37.2 billion, comScore said. In the face of continued economic uncertainty, online spending is projected to climb 17% this season to $54.47 billion, according to MarketLive. “It’s very important for any retailer to have a web presence or you risk being left out in the cold,” said Andrew Lipsman, vice president of industry analysis at comScore, who noted that even in-person purchases typically originate online. Adapting to Shifting Threat Security professionals believe retailers’ cyber defenses are more porous than those of financial institutions — and even some banks succumbed to relentless DDoS attacks this fall. Given their prior experience combating thieves in Russia and elsewhere trying to siphon funds or snatch credit-card numbers, retailers aren’t really positioned to halt massive DDoS attacks from powerful state actors like Iran. “That’s a very different threat and in many ways is more severe,” said Aitel. “They’re not thinking: What if it’s not about the money? What if someone wants to take me out just to take me out?” Cedric Leighton, a former NSA official, said he agrees that retailers are not as well prepared as their financial peers. “I don’t think they’ve gotten to the point where they can truly say their whole cyber supply chain is as well secured as they need to be in this day and age,” said Leighton, CEO of a Washington, D.C.-based risk-management consultancy. Leighton said hackers could also disrupt companies’ supply chains by messing with order quantities and locations, creating costly problems for retailers. Just this week Barnes & Noble (BKS) fell victim to a very sophisticated criminal attack that may have resulted in stolen credit and debit card information at 63 of its stores. Amazon Atop Target List The importance of a robust cyber defense is even more important for online retailers like Amazon.com and Overstock (OSTK). “If they aren’t available online, there is no business. They don’t exist,” said Ronen Kenig, director of security product marketing at Tel Aviv-based security firm Radware (RDWR). In a potential cyber attack on U.S. retailers, Amazon.com would clearly be the biggest prize. The Seattle company generated $17.4 billion in revenue last holiday quarter. “When you attack the United States you don’t attack Topeka, Kansas,” said Aitel. “Amazon is the big boy on the block. They are of course also the best protected.” Amazon.com and Wal-Mart (WMT) declined to comment for this story, while Target (TGT) didn’t respond to a request for comment. “Every company is going to look at what its exposure is. The greater the company is placed at risk, then the more they are going to invest in trying to protect themselves,” said Mallory Duncan, general counsel at the National Retail Federation. Noting that some companies “rely extremely heavily on the Internet,” Duncan said, “When you have a bet-the-company type of situation, they’re going to take extraordinary steps to protect that channel.” Cyber Monday in Focus Aitel suggested the days around Cyber Monday — the first work day after Black Friday — as a time when retailers need to be particularly vigilant about the cyber threat. According to comScore, U.S. e-commerce spending on Cyber Monday rose 22% last year to $1.25 billion, making it the highest online spending day in history. “The attackers always like to choose the worst time for the victim,” said Kenig. Bolstering Cyber Defenses So what specifically should retailers be doing to prevent or mitigate the impact of DDoS attacks this holiday season? Leighton said it’s crucial for companies to implement redundant systems with backups that allow switching from one system to the other when necessary. From a bigger picture standpoint, retailers should strive to install security programs that go above and beyond industry security standards, which Aitel said “are really the bottom bar.” Security professionals have been particularly alarmed by some recent cyber attacks that inflicted damage on physical assets, including a devastating attack unleashed on Saudi Arabia’s state run oil company Saudi Aramco Some believe Iran may have been behind this attack, which destroyed an estimated 30,000 computers. Aitel said, “Companies have to look at what happened to Saudi Aramco and say: What would we do if that happened to us? Until they have a good answer for that, they shouldn’t be sleeping that well.” For advanced DDoS protection against your eCommerce site click here . Source: http://www.foxbusiness.com/industries/2012/10/24/would-cyber-attacks-ruin-christmas-for-retailers/
A string of cyber attacks on U.S. financial institutions has created headaches this fall by slowing down or preventing online banking access for millions of Americans. But imagine the real economic damage that similar-style attacks would cause if they struck U.S. retailers this holiday-shopping season, potentially eating into projected online sales of $54 billion. While retailers deserve credit for bolstering their defenses against credit-card-hungry organized crime rings, security professionals believe the industry is vulnerable to this different kind of onslaught aimed at crippling online sales. “The gloves are off in cyber space. The reality is if they want it to get worse, it can get worse,” said Dave Aitel, a former computer scientist at the National Security Agency. “I don’t think people are really prepared mentally to what happens if Amazon goes down.” Unlike the ongoing cyber attacks against U.S. banks, there doesn’t appear to be a specific cyber threat against retailers. Yet there are concerns that retailers aren’t ready for denial-of-service (DDoS) attacks from a powerful state actor like Iran, which many in the U.S. government suspect had a hand in the recent attacks on financial institutions like Bank of America (BAC) and J.P. Morgan Chase (JPM). “The Iranians are in the business of making a point and the bank attacks are not likely to have the impact they need, hence retailers are the next most likely target, especially in the holiday season,” said Aitel, CEO of Immunity, a cyber security firm that works with Fortune 500 companies. Online Sales Exceed $160B It’s hard to overstate the importance of e-commerce in today’s smartphone and social network dominated world. According to comScore (CSOR), annual U.S. retail e-commerce spending has surged 143% since 2004 to $161.52 billion last year. Despite the sluggish domestic economy and tepid retail sales growth, e-commerce spending jumped 13% between 2010 and 2011. Online shopping is crucial during the all-important holiday-shopping season. E-commerce spending rose 14% last holiday season to $37.2 billion, comScore said. In the face of continued economic uncertainty, online spending is projected to climb 17% this season to $54.47 billion, according to MarketLive. “It’s very important for any retailer to have a web presence or you risk being left out in the cold,” said Andrew Lipsman, vice president of industry analysis at comScore, who noted that even in-person purchases typically originate online. Adapting to Shifting Threat Security professionals believe retailers’ cyber defenses are more porous than those of financial institutions — and even some banks succumbed to relentless DDoS attacks this fall. Given their prior experience combating thieves in Russia and elsewhere trying to siphon funds or snatch credit-card numbers, retailers aren’t really positioned to halt massive DDoS attacks from powerful state actors like Iran. “That’s a very different threat and in many ways is more severe,” said Aitel. “They’re not thinking: What if it’s not about the money? What if someone wants to take me out just to take me out?” Cedric Leighton, a former NSA official, said he agrees that retailers are not as well prepared as their financial peers. “I don’t think they’ve gotten to the point where they can truly say their whole cyber supply chain is as well secured as they need to be in this day and age,” said Leighton, CEO of a Washington, D.C.-based risk-management consultancy. Leighton said hackers could also disrupt companies’ supply chains by messing with order quantities and locations, creating costly problems for retailers. Just this week Barnes & Noble (BKS) fell victim to a very sophisticated criminal attack that may have resulted in stolen credit and debit card information at 63 of its stores. Amazon Atop Target List The importance of a robust cyber defense is even more important for online retailers like Amazon.com and Overstock (OSTK). “If they aren’t available online, there is no business. They don’t exist,” said Ronen Kenig, director of security product marketing at Tel Aviv-based security firm Radware (RDWR). In a potential cyber attack on U.S. retailers, Amazon.com would clearly be the biggest prize. The Seattle company generated $17.4 billion in revenue last holiday quarter. “When you attack the United States you don’t attack Topeka, Kansas,” said Aitel. “Amazon is the big boy on the block. They are of course also the best protected.” Amazon.com and Wal-Mart (WMT) declined to comment for this story, while Target (TGT) didn’t respond to a request for comment. “Every company is going to look at what its exposure is. The greater the company is placed at risk, then the more they are going to invest in trying to protect themselves,” said Mallory Duncan, general counsel at the National Retail Federation. Noting that some companies “rely extremely heavily on the Internet,” Duncan said, “When you have a bet-the-company type of situation, they’re going to take extraordinary steps to protect that channel.” Cyber Monday in Focus Aitel suggested the days around Cyber Monday — the first work day after Black Friday — as a time when retailers need to be particularly vigilant about the cyber threat. According to comScore, U.S. e-commerce spending on Cyber Monday rose 22% last year to $1.25 billion, making it the highest online spending day in history. “The attackers always like to choose the worst time for the victim,” said Kenig. Bolstering Cyber Defenses So what specifically should retailers be doing to prevent or mitigate the impact of DDoS attacks this holiday season? Leighton said it’s crucial for companies to implement redundant systems with backups that allow switching from one system to the other when necessary. From a bigger picture standpoint, retailers should strive to install security programs that go above and beyond industry security standards, which Aitel said “are really the bottom bar.” Security professionals have been particularly alarmed by some recent cyber attacks that inflicted damage on physical assets, including a devastating attack unleashed on Saudi Arabia’s state run oil company Saudi Aramco Some believe Iran may have been behind this attack, which destroyed an estimated 30,000 computers. Aitel said, “Companies have to look at what happened to Saudi Aramco and say: What would we do if that happened to us? Until they have a good answer for that, they shouldn’t be sleeping that well.” For advanced DDoS protection against your eCommerce site click here . Source: http://www.foxbusiness.com/industries/2012/10/24/would-cyber-attacks-ruin-christmas-for-retailers/